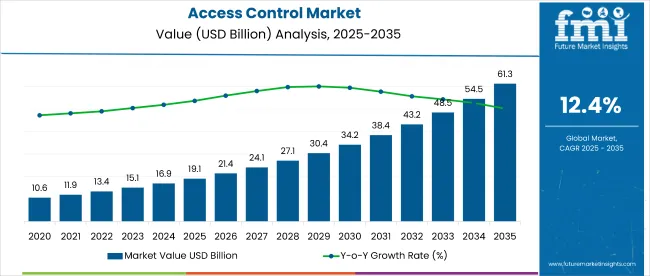
Access control industry valuation is set to reach USD 21.5 billion in 2026, driven by escalating cybersecurity threats and growing demand for advanced identity management solutions across enterprise environments. Revenue from access control system sales is projected to expand at a CAGR of 12.8% through 2036, pushing total sector worth beyond USD 71.2 billion by the end of the forecast period. Accelerating enterprise digital transformation initiatives and tightening regulatory compliance requirements continue to act as primary growth catalysts.
Manufacturers are channeling substantial investment into biometric and multi-modal authentication technologies, integrating artificial intelligence and machine learning to enhance authentication accuracy without compromising system performance. Product developers are increasingly shifting away from traditional card-based access models toward identity-centric and behavioral authentication frameworks, particularly across financial institutions, government facilities, and critical infrastructure environments. Reflecting this strategic shift, Microsoft Chairman and CEO Satya Nadella emphasized the importance of modern security architectures, stating, “Zero Trust is at the foundation of security transformation and organizational resilience in the face of major cybersecurity threats.”
Rising awareness of insider threats and credential compromise incidents is further accelerating adoption of risk-based authentication and continuous verification approaches. Organizations are prioritizing identity governance platforms capable of enforcing contextual access policies across hybrid IT environments and distributed workforces. Cloud-native access control solutions are gaining strong momentum as enterprises seek scalable, software-defined security perimeters aligned with remote and hybrid operating models.
Government regulations are also playing a decisive role in shaping demand dynamics. Zero-trust mandates, stricter data protection regulations, and critical infrastructure security frameworks increasingly require multi-factor authentication, privileged access management, and continuous identity monitoring. As per FMI’s projection, the convergence of regulatory pressure with cloud-first security strategies will accelerate adoption of intelligent, identity-driven access control architectures over the forecast period.
| Metric | Value |
|---|---|
| Industry Size (2026) | USD 21.5 Billion |
| Industry Value (2036) | USD 71.2 Billion |
| CAGR (2026-2036) | 12.8% |
Source: Future Market Insights’ proprietary forecasting model and primary research
Hardware-led access control adoption is best tracked through technology KPIs that link revenue quality, customer outcomes, and system performance. On the financial side, recurring revenue strength is reflected in MRR and improved unit economics through LTV versus CAC, while lower churn signals durable deployment value. Customer success momentum shows up in higher NPS, stronger retention, and deeper user engagement, especially as enterprises standardize biometric and tamper-resistant devices. Product performance is validated through higher uptime, faster response time, and better conversion rate from enrollment to successful authentication. Execution capability is reinforced by software development metrics such as velocity, cycle time, deployment frequency, and MTTR, enabling rapid firmware and security updates. Finally, IT operations maturity is tracked through fewer security incidents, lower incident rates, and faster ticket resolution time across sites.
Global landscape is intricately segmented to address diverse requirements of the enterprise security industry, categorizing sector by component type, system architecture, end-user vertical, and deployment model. Structural division allows stakeholders to identify specific threat mitigation targets, such as rising demand for cloud-based identity platforms in remote workforce scenarios or preference for on-premises biometric systems in classified government applications. By analyzing these segments, manufacturers can tailor development strategies to meet distinct needs of enterprise IT departments versus physical security teams. Segmentation also highlights transition from perimeter-based security approaches to identity-centric protection frameworks. As industry matures, granular segmentation becomes essential for understanding threat landscapes and compliance requirements, ensuring solution development aligns with evolving cybersecurity standards.
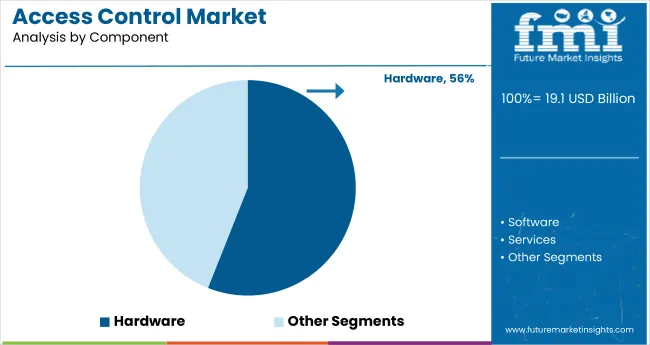
Hardware retains a 58.2% share in 2026 because access control programs are still budgeted and delivered around the physical layer: readers, controllers, locks, door hardware, secure credential interfaces, and tamper supervision. Large refresh cycles are being pulled by controller upgrades, encrypted reader connectivity, and higher-assurance edge devices that can enforce secure boot, signed firmware, and protected key storage at the panel or reader level.
Another reinforcing factor is the move from legacy Wiegand and basic interfaces toward OSDP Secure Channel style deployments, which typically requires replacing readers, upgrading panels, and reworking device communications. That is a hardware-led scope expansion, not a software-only uplift, so component revenue stays concentrated in endpoints and control hardware rather than shifting entirely into platforms.
FMI is of the opinion that hardware share will stay elevated as enterprises standardize on edge-verified identity checks, stronger tamper signaling, and cryptographic protection at the device, especially in multi-site rollouts where physical attack surface and maintenance realities drive procurement decisions.
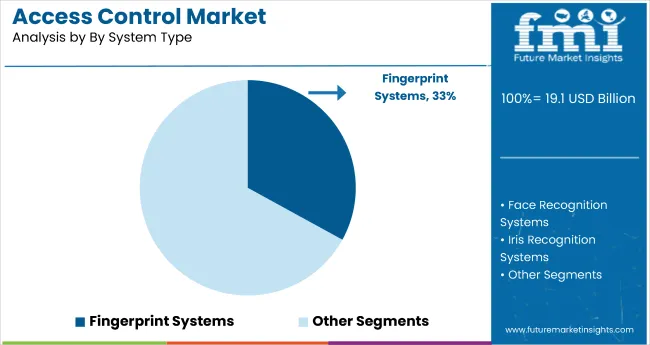
Iris recognition leads the system type category with a 37.4% share in 2026 because it is frequently selected for high-assurance zones where operators want high accuracy at low false-accept settings and contactless operation without the hygiene and wear concerns associated with touch-based biometrics. Adoption is also supported by deployment patterns that demand controlled enrollment, consistent lighting management, near-infrared capture, and hardened template protection workflows.
Preference is strongest where integrators must specify robust anti-spoof controls using presentation-attack defense requirements aligned to widely used biometric security evaluation concepts. That keeps iris solutions positioned as a premium, security-led choice rather than a convenience-led modality.
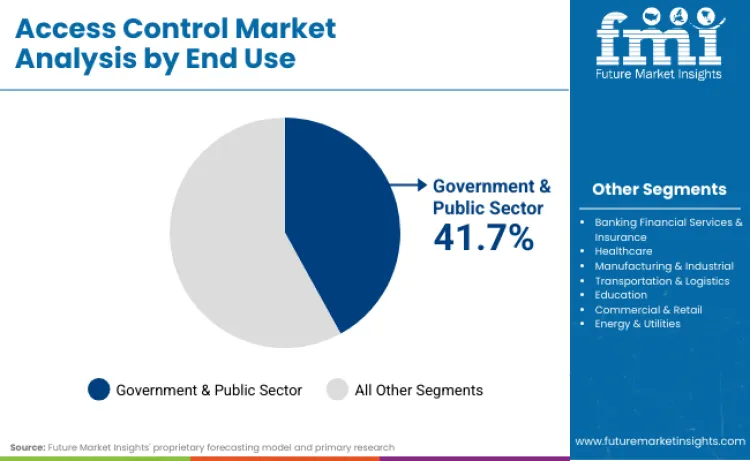
Government applications hold 41.7% share in 2026 because procurement is driven by assurance frameworks and audit requirements, not just door throughput. Programs often require multi-factor policy, centralized identity proofing alignment, strong credential lifecycle controls, and forensic-grade event logging that can be correlated across sites and systems.
Government buyers also prioritize validated cryptography, certified components, and interoperability with credential standards and clearance-linked access workflows. That pushes deployments toward higher-spec controllers, hardened readers, and certified encryption stacks, which increases spend per opening and sustains higher ASPs for compliant solutions.
In 2025, many enterprises treated Zero Trust as a roadmap item and ran partial pilots around identity, VPN replacement, or conditional access. In 2026, the shift is that Zero Trust becomes an operating model where every access decision is evaluated continuously, using policy decision and enforcement points aligned to the NIST Zero Trust reference model. That change pulls more spend into access control platforms that can ingest risk signals in real time and enforce policy consistently across users, devices, and locations, especially where physical access events must be correlated with cyber identity posture.
This pushes vendors away from simple door credential checks and toward policy-driven access that integrates with identity providers, endpoint telemetry, and SOC workflows. FMI is of the opinion that in 2026, enterprise buyers will increasingly score vendors on whether they can operationalize the Zero Trust control loop, not whether they simply “support” Zero Trust as a feature set.
Compared with 2025, 2026 is more audit-real than policy-discussion. In Europe, NIS2 has already moved from directive to national transposition deadlines, so organizations in scope are under pressure to evidence governance, controls, and incident-readiness. In financial services, DORA entered into application on 17 January 2025, making 2026 a full operating year where resilience controls, third-party risk registers, and testing expectations materially influence procurement for access control, identity, and monitoring.
In the US, the SEC’s cybersecurity disclosure rules keep raising the cost of weak evidence: when material incidents require structured disclosure, buyers place higher value on access systems that produce defensible audit trails, time-synchronized logs, and clear accountability for privileged access and policy exceptions. The practical 2026 effect is that innovation concentrates on features that survive audit: immutable logging, strong cryptographic controls, controlled biometric data handling, and compliance-ready reporting, not just UI improvements.
In 2025, AI in access control often meant better analytics and anomaly flags. In 2026, the center of gravity shifts to governed AI, because regulatory expectations around AI risk and documentation tighten and global frameworks mature. The EU AI Act timeline points to high-risk obligations coming into scope from August 2026, which raises the bar for how AI-driven access decisions are explained, logged, and monitored. At the same time, ISO/IEC 42001:2023 gives organizations a management-system path for AI governance, and that becomes relevant when access decisions are influenced by model outputs.
For vendors, this means AI features must be built for auditability: decision traceability, model change control, and clear separation between advisory risk scoring and enforcement logic. FMI is of the opinion that the 2026 winners will be the platforms that can prove “why access was allowed or denied” in a way that stands up to compliance reviews, not just SOC dashboards.
Global landscape for access control technology is characterized by diverse regulatory environments, influenced by national security frameworks and privacy protection standards. Established markets prioritize advanced biometric systems and AI-powered threat detection, whereas emerging economies focus on cost-effective authentication solutions and basic access management capabilities. North America is emerging as innovation leader due to zero trust architecture adoption and cybersecurity investment priorities. Conversely, Asia-Pacific markets pivot towards mobile-first authentication and cloud-native identity platforms. Government initiatives in developed nations supporting critical infrastructure protection ensure sustained demand for high-assurance access control solutions across all security-sensitive sectors.
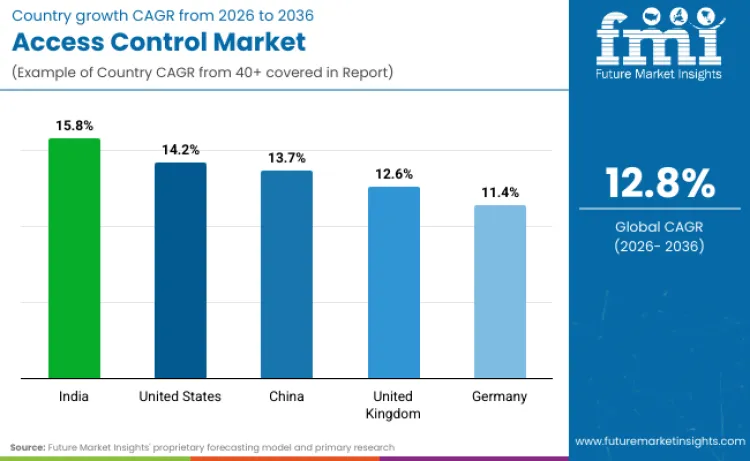
| Country | CAGR (2026 to 2036) |
|---|---|
| United States | 14.2% |
| China | 13.7% |
| India | 15.8% |
| Germany | 11.4% |
| United Kingdom | 12.6% |
Source: Future Market Insights analysis, supported by a proprietary forecasting model and primary research
Sales of access control systems in United States are set to grow at 14.2% CAGR through 2036. Expansion is underpinned by federal direction to strengthen cybersecurity posture across agencies and suppliers, with clear emphasis on modern identity practices, software supply chain assurance, and stronger authentication. Executive Order 14028 focuses federal action on improving national cybersecurity and supply chain security, which raises baseline expectations for identity and access governance in both public sector and contractor environments. CISA also frames the executive order implementation around adoption of zero trust approaches and deployment of multifactor authentication, reinforcing investment in access control modernization that ties physical entry, identity verification, and centralized policy control into enterprise security programs. In addition, NIST approval of post quantum cryptography FIPS standards signals a longer runway of security modernization planning that can influence procurement roadmaps for identity systems that must remain robust over extended lifecycles.
Demand for access control solutions in China is projected to rise at 13.7% CAGR during the assessment period. Expansion is supported by digital economy priorities that encourage connected infrastructure, including smart governance and integrated digital services. The State Council has issued guidance tied to 14th Five Year Plan era goals for digital economy development, which supports broader deployment of connected systems across cities and public services. At the same time, the regulatory environment places stronger obligations on data processing and personal information handling, which affects how biometric identity systems are designed, stored, and governed. China’s Data Security Law and the Personal Information Protection Law provide core legal anchors that push implementers toward tighter controls, auditability, and localized compliance alignment for identity related deployments. FMI is of the opinion that China’s policy driven digital infrastructure buildout will continue to expand demand for integrated physical and digital access control platforms, especially where compliance requirements shape system design choices.
Access control industry in India is poised to expand at 15.8% CAGR. Growth is largely attributed to rapid digitization across banking, enterprise services, and large institutions, supported by a national foundation for digital delivery of services. Digital India is positioned as a flagship government program aimed at transforming India into a digitally empowered society and knowledge economy, supporting broader adoption of digital identity and verification aligned services. Aadhaar based authentication is widely defined by UIDAI as a verification process that can use demographic or biometric information, which normalizes biometric verification expectations across multiple sectors. UIDAI also specifies requirements around biometric devices used for Aadhaar authentication, reinforcing ecosystem standardization that indirectly supports enterprise adoption of biometric capable access control hardware and integration practices.
Sales of access control systems in Germany are set to grow at 11.4% CAGR. Expansion is underpinned by compliance driven cybersecurity and resilience expectations across critical sectors and industrial environments, where secure identity enforcement is increasingly tied to operational continuity. The EU NIS2 Directive strengthens cybersecurity requirements across a wider set of sectors in the Union, increasing pressure on covered entities to implement stronger controls and governance, including access management related capabilities. Germany’s cybersecurity posture is also shaped by national security legislation updates described by the BSI under the IT Security Act 2.0, which supports higher baseline expectations for secure components and protection of critical systems. FMI is of the opinion that Germany’s industrial compliance culture will keep driving demand for access control systems that prioritize documentation, privacy alignment, and secure integration with industrial and facility management systems.
Revenue from access control systems in United Kingdom is set to grow at 12.6% CAGR. Expansion is underpinned by regulated sector emphasis on operational resilience and secure service delivery, particularly in financial services, alongside public sector modernization. The FCA has set out final rules and guidance on building operational resilience, creating sustained demand for security systems that can support continuity, governance, monitoring, and recovery expectations across important business services. In the public sector, the Government Cloud First policy directs departments to consider public cloud services as the first choice in technology decisions, which supports adoption of centrally managed and remotely administered security platforms where appropriate.
Competition in the access control space is increasingly shaped by how well vendors connect door hardware, credentials, video feeds, and incident workflows into a single, manageable platform. Enterprises are looking for fewer dashboards and tighter audit trails, so providers are positioning access control as part of a unified security environment rather than a standalone system. Cloud and hybrid deployment models are gaining attention because they allow centralized credential management across multiple sites without replacing existing on-premise infrastructure.
Vendors are also differentiating through authentication approaches. Mobile credentials, biometrics, and standards-based identity methods are being promoted to reduce dependence on physical cards while improving assurance levels. Integration with enterprise identity and cybersecurity tools is becoming a common requirement in procurement, pushing access control providers to align more closely with IT security teams.
From a go-to-market perspective, brands are focusing on system integrator partnerships, certified installer networks, and vertical targeting of airports, data centers, commercial buildings, and industrial facilities where compliance and monitoring are critical. Portfolio positioning varies as well: some players emphasize credential and reader technologies, while others lead with door hardware and physical locking ecosystems. FMI is of the opinion that platform integration, flexible deployment, and authentication strength will remain central to competitive differentiation in this market.
| Items | Values |
|---|---|
| Quantitative Units | USD Billion |
| Component Segments | Hardware (Biometric Scanners, Smart Cards, Controllers, Electronic Locks); Software (Access Control Management Software, Identity Management Platforms, Analytics Software); Services (Installation & Integration, Maintenance & Support, Consulting Services) |
| System Type Categories | Iris Recognition Access Control Systems; Fingerprint Access Control Systems; Face Recognition Access Control Systems; Card-Based Access Control Systems; Voice Recognition Access Control Systems; Multi-Modal Biometric Systems |
| End-User Industry Categories | Government & Public Sector; Banking Financial Services & Insurance; Healthcare; Manufacturing & Industrial; Transportation & Logistics; Education; Commercial & Retail; Energy & Utilities |
| Deployment Model Types | On-Premises; Cloud-Based; Hybrid; Software-as-a-Service (SaaS) |
| Regions Covered | North America, Europe, Asia-Pacific, Latin America, Middle East & Africa |
| Key Countries | United States, China, India, Germany, United Kingdom |
| Key Companies Profiled | Honeywell International Inc.; Johnson Controls; Assa Abloy AB; HID Global Corporation; Dormakaba Holding AG; Bosch Security Systems; NEC Corporation; Thales Group; Stanley Security; Identiv Inc. |
| Additional Attributes | Dollar sales measured for access control systems used in enterprise security and identity management applications, specified by component type (hardware/software/services), system architecture (biometric/card-based/mobile), end-user industry, deployment model (on-premises vs. cloud), and compliance alignment with evolving cybersecurity regulations and identity governance standards. |
How big is the global access control market?
The global access control market is valued at USD 21.5 billion in 2026.
What is the growth outlook for the access control market over the next 10 years?
The market is forecast to grow at a 12.8% CAGR from 2026 to 2036, reaching USD 71.2 billion.
Which industries or use cases drive adoption?
Adoption is driven by government and public sector security, BFSI identity protection, critical infrastructure, enterprise workplaces, and high-assurance facilities requiring biometric authentication.
How does adoption differ by region or maturity level?
Adoption is led by North America and Europe through zero trust and regulatory-driven deployments, while Asia-Pacific shows faster growth from digital government, smart city, and cloud-first identity programs.
What are the main barriers to adoption or scaling?
Key barriers include high upfront hardware costs, system integration complexity, privacy concerns around biometrics, and legacy infrastructure compatibility.
Full Research Suite comprises of:
Market outlook & trends analysis
Interviews & case studies
Strategic recommendations
Vendor profiles & capabilities analysis
5-year forecasts
8 regions and 60+ country-level data splits
Market segment data splits
12 months of continuous data updates
DELIVERED AS:
PDF EXCEL ONLINE
Thank you!
You will receive an email from our Business Development Manager. Please be sure to check your SPAM/JUNK folder too.