BYOD Security Market : Global Industry Analysis 2015 - 2024 and Opportunity Assessment 2025 - 2035
BYOD Security Market Size and Share Forecast Outlook 2025 to 2035
Historical Data Covered: 2015 - 2024 | Base Year: 2024 | Estimated Year: 2025 | Forecast Period: 2025 - 2035
BYOD Security Market Size and Share Forecast Outlook 2025 to 2035
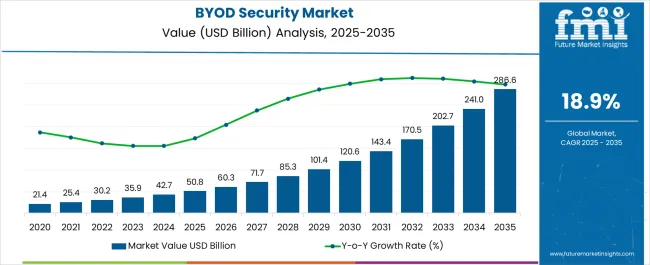
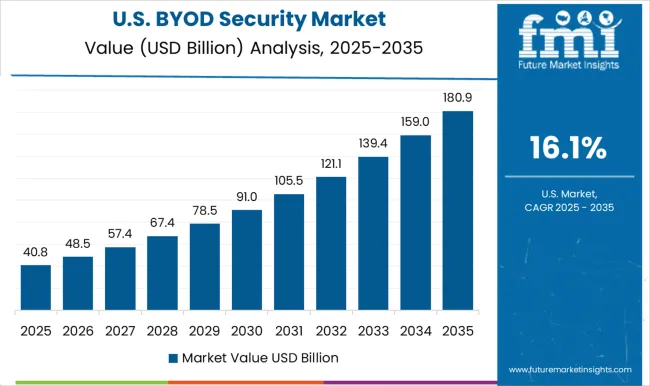
The BYOD Security Market is estimated to be valued at USD 50.8 billion in 2025 and is projected to reach USD 286.6 billion by 2035, registering a compound annual growth rate (CAGR) of 18.9% over the forecast period.
Quick Stats for BYOD Security Market
- BYOD Security Market Industry Value (2025): USD 50.8 billion
- BYOD Security Market Forecast Value (2035): USD 286.6 billion
- BYOD Security Market Forecast CAGR: 18.9%
- Leading Segment in BYOD Security Market in 2025: Laptop (48.6%)
- Key Growth Region in BYOD Security Market: North America, Asia-Pacific, Europe
- Top Key Players in BYOD Security Market: IBM, Quokka, Palo Alto Networks, Qualcomm, Zimperium, NIST, Intel, Lenovo
| Metric | Value |
|---|---|
| BYOD Security Market Estimated Value in (2025 E) | USD 50.8 billion |
| BYOD Security Market Forecast Value in (2035 F) | USD 286.6 billion |
| Forecast CAGR (2025 to 2035) | 18.9% |
Rationale for Segmental Growth in the BYOD Security Market
The BYOD security market is experiencing strong momentum driven by the rapid adoption of remote and hybrid work models, alongside the rising penetration of personal devices in enterprise networks. The increasing frequency of cyber threats and data breaches has compelled organizations to prioritize robust security frameworks that can safeguard sensitive information across diverse endpoints.
Growing regulatory pressure regarding data protection and compliance has also accelerated the adoption of advanced security solutions. Continuous innovations in authentication technologies, encryption, and mobile device management are further strengthening the market.
With enterprises focusing on achieving higher operational flexibility without compromising on security, the outlook for BYOD security remains favorable, supported by continued digital transformation initiatives across industries.
Segmental Analysis
The market is segmented by Device Type and Solution Type and region. By Device Type, the market is divided into Laptop, Tablet, and Smartphone. In terms of Solution Type, the market is classified into Mobile Data Security, Mobile Device Security, and Network Security. Regionally, the market is classified into North America, Latin America, Western Europe, Eastern Europe, Balkan & Baltic Countries, Russia & Belarus, Central Asia, East Asia, South Asia & Pacific, and the Middle East & Africa.
Insights into the Laptop Device Type Segment
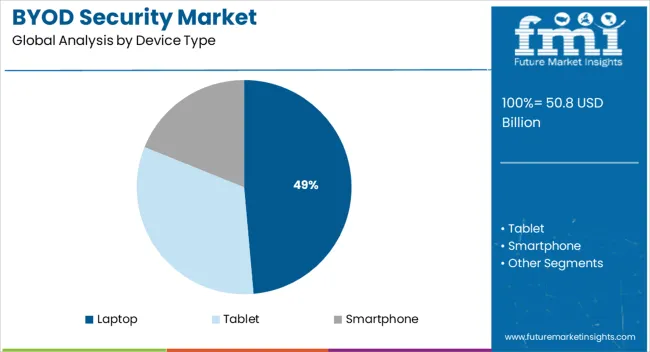
The laptop device type segment is projected to hold 48.60% of the overall market revenue by 2025, establishing it as the leading category. This prominence is attributed to the widespread use of laptops in enterprise operations and their central role in accessing sensitive corporate applications and data.
The reliance on laptops for high performance computing, collaboration, and remote working has necessitated advanced endpoint security measures. Additionally, the greater exposure of laptops to phishing, malware, and ransomware attacks compared to other devices has reinforced the demand for comprehensive protection strategies.
As organizations continue to integrate remote and mobile workforces, laptops remain the dominant device category driving security investments.
Insights into the Mobile Data Security Solution Type Segment
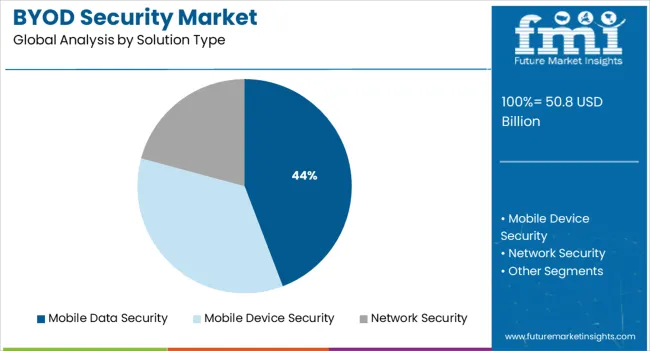
The mobile data security solution type segment is anticipated to account for 44.20% of total market revenue by 2025, positioning it as the largest within its category. The growth of this segment is being propelled by the surge in mobile device usage for both personal and professional tasks, creating heightened risks of data leaks and unauthorized access.
Organizations are increasingly investing in encryption, secure containers, and advanced mobile threat defense tools to protect corporate data on employee devices. The ability to monitor, manage, and secure mobile endpoints has become essential in reducing vulnerabilities across bring your own device environments.
As mobile devices continue to be integral to enterprise productivity, mobile data security solutions are expected to maintain their leadership in ensuring safe and compliant BYOD practices.
2020 to 2025 BYOD Security Market Demand Outlooks Compared to 2025 to 2035 Forecast
The CAGR for BYOD security market is expected to grow from 13.0% in 2020-22 to 18.9% in 2025 to 2035.
Around three out of every five employees under the age of 25, as well as more than half of those over the age of 30, say that the technology they use at home is superior to the tools available at work. BYOD emerged as a subset of the greater trend of IT consumerisation, in which software and hardware from the consumer realm are permitted into business premises.
This market is still in its growth stage and therefore can provide great opportunities for investors.
The CAGR for BYOD security market is expected to grow from 13.0% in 2020-22 to 18.9% in 2025 to 2035.
Around three out of every five employees under the age of 25, as well as more than half of those over the age of 30, say that the technology they use at home is superior to the tools available at work. BYOD emerged as a subset of the greater trend of IT consumerisation, in which software and hardware from the consumer realm are permitted into business premises.
This market is still in its growth stage and therefore can provide great opportunities for investors.
BYOD offers cost savings and ease by allowing employees to use endpoints for work-related purposes.
BYOD has various business advantages, like cost savings and ease. By implementing BYOD, businesses may improve their flexibility, mobility, and productivity. Businesses that use BYOD programmes in their offices do not need to purchase new devices or carrier plans for each employee.
Each employee is free to utilise the endpoints that they possess for work-related purposes. Some businesses may choose to pay their staff with a compensation that covers a portion or the entirety of their phone expenses.
Others may provide payment based on the employee's geographic area and the price of terminal ownership. BYOD's low cost is a key positive for firms that really are looking to implement a portability programme or are just getting started.
This market is still in introductory phase and will provide great opportunities for early investors.
Regional Analysis
Due to the widespread use of BYOD security system, North America dominates the global market for BYOD security with a market share of 28.4%.
Increasing investment in wireless technology development, a strong presence of major industry players, and growing preference for personalized workspace are some of the primary drivers driving revenue growth in this region.
Country wise insights
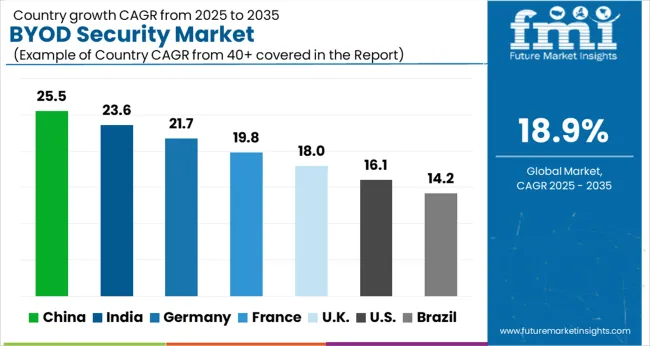
Corporations in USA collaborate to develop mobile security framework for BYOD security administration
BYOD is becoming popular in companies in the USA, with several employees preferring to bring their own devices to work. This has however lead to the problem of maintaining confidentiality with these employees owned devices, in light of these events IBM, Quokka, Palo Alto Networks, Qualcomm, Zimperium have decided to collaborate with NIST to develop Mobile Security Framework, which is a framework developed for BYOD Security administration, which can be followed by companies in the US wanting to implement BYOD.
Therefore, USA held the largest market share of 24.2%in 2025.
The demand for BYOD security is being driven by Indian companies' need for BYOD device cybersecurity
The BYOD Security is still emerging in India; the companies that allow BYOD tend to adopt this model to cut costs and therefore dont seem to be affected by security concerns. On the other hand companies that are tight in security prefer to provide employees with work computers or use alternative models like company-owned, business-only (COBO), and company-owned, personally-enabled (COPE). However, some companies have started to see the advantage of BYOD and are planning to implement it, such companies are likely to require cybersecurity systems for their devices creating demand for BYOD security in the future.
Therefore, India has a CAGR of 17.3%for the BYOD security market over the forecast period.
UAE firms are trying to implement BYOD security applications to boost employee productivity, creating opportunities for BYOD security market
According to Al-Tamimi, a UAE-based legal firm, consumers spend 3 times more on IT than corporations - smartphone adoption in the Emirati is higher than in the US. Taking advantage of the prevalence of mobile devices can boost employee productivity. UAE based firms are therefore trying to implement BYOD security applications, creating opportunities for BYOD security market in UAE,
Thus these factors allow UAE to hold a market share of 19.2%.in 2025 for the BYOD security market.
Category wise Insights
Is There a Growth Opportunity in BYOD Security for Laptops?
Laptops are most commonly the devices used in BYOD models as they are the most common form of personal work computers, this has led to several security techniques being developed for laptop security, such as biometric identification, smart cards and other encryption methods. These methods however restrict usage of the laptop on a personal level and therefore may not be preferable for BYOD Security. This creates an opportunity for research and development in the BYOD security for laptops fields, giving it a CAGR of 17.6%
Is Mobile Data Security a profitable market to invest in?
Bringing personal devices to work brings the challenge for maintaining company confidentiality, container applications are one method for allowing employees to utilise their own devices while also minimising security threats. These are usually provided by third-party vendors. One container can contain several apps. This option gives the employee less control over their device while still offering appropriate security controls and monitoring. Therefore, Mobile Data Security is a profitable market to invest in.
These factors lead mobile data security to have the CAGR of 16.9% over the given forecast period.
Competitive Landscape
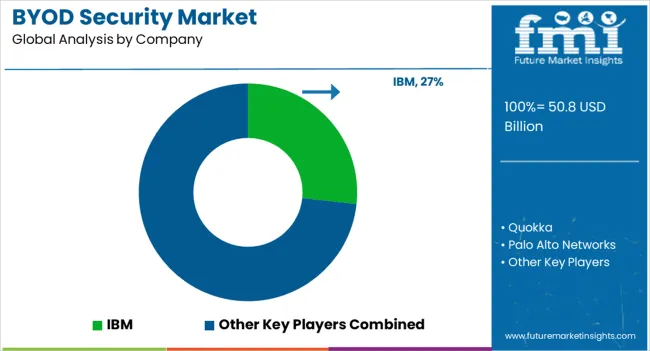
Several Companies in both developed and developing countries are emerging in the BYOD security market, this is leading the market into a position of competitiveness as no firms have been established as a top player yet.
- In November 2025, IBM, Quokka, Palo Alto Networks, Qualcomm, Zimperium have decided to collaborate with NIST to develop Mobile Security Framework, which is a framework developed for BYOD Security administration.
- In January 2025, Intel introduces a secure computing platform for virtual machines. Intel's VM isolation solution is intended to safeguard data kept within VMs within a trusted runtime environment that is separate from the underlying hardware.
Scope of report
| Attribute | Details |
|---|---|
| Market value in 2025 | USD 50.8 billion |
| Market CAGR 2025 to 2035 | 18.9% |
| Share of top 5 players | 20.5% |
| Forecast Period | 2025 to 2035 |
| Historical Data Available for | 2020 to 2025 |
| Market Analysis | USD Billion for Value |
| Key Regions Covered | North America; Latin America; Europe; South Asia Pacific; East Asia and the Middle East Africa |
| Key Countries Covered | USA, Canada, Germany, UK, France, Italy, Spain, Russia, China, Japan, South Korea, India, Australia New Zealand, GCC Countries, Turkey and South Africa |
| Key Segments Covered | Device Type, Solution Type and Region |
| Key Companies Profiled | IBM; Quokka; Palo Alto Networks; Qualcomm; Zimperium; NIST; Intel; Lenovo |
| Report Coverage | Market Forecast, Company Share Analysis, Competition Intelligence, DROT Analysis, Market Dynamics and Challenges, and Strategic Growth Initiatives |
| Customization Pricing | Available upon Request |
BYOD Security by Category
By Device Type:
- Laptop
- Tablet Smartphone
By Solution Type:
- Mobile Data Security
- Mobile Device Security
- Network Security
By Region:
- North America
- Latin America
- Europe
- East Asia
- South Asia and Pacific
- Middle East and Africa
Frequently Asked Questions
How big is the byod security market in 2025?
The global byod security market is estimated to be valued at USD 50.8 billion in 2025.
What will be the size of byod security market in 2035?
The market size for the byod security market is projected to reach USD 286.6 billion by 2035.
How much will be the byod security market growth between 2025 and 2035?
The byod security market is expected to grow at a 18.9% CAGR between 2025 and 2035.
What are the key product types in the byod security market?
The key product types in byod security market are laptop, tablet and smartphone.
Which solution type segment to contribute significant share in the byod security market in 2025?
In terms of solution type, mobile data security segment to command 44.2% share in the byod security market in 2025.
Table of Content
- Executive Summary
- Global Market Outlook
- Demand-side Trends
- Supply-side Trends
- Technology Roadmap Analysis
- Analysis and Recommendations
- Market Overview
- Market Coverage / Taxonomy
- Market Definition / Scope / Limitations
- Market Background
- Market Dynamics
- Drivers
- Restraints
- Opportunity
- Trends
- Scenario Forecast
- Demand in Optimistic Scenario
- Demand in Likely Scenario
- Demand in Conservative Scenario
- Opportunity Map Analysis
- Product Life Cycle Analysis
- Supply Chain Analysis
- Investment Feasibility Matrix
- Value Chain Analysis
- PESTLE and Porter’s Analysis
- Regulatory Landscape
- Regional Parent Market Outlook
- Production and Consumption Statistics
- Import and Export Statistics
- Market Dynamics
- Global Market Analysis 2020 to 2024 and Forecast, 2025 to 2035
- Historical Market Size Value (USD Million) Analysis, 2020 to 2024
- Current and Future Market Size Value (USD Million) Projections, 2025 to 2035
- Y-o-Y Growth Trend Analysis
- Absolute $ Opportunity Analysis
- Global Market Pricing Analysis 2020 to 2024 and Forecast 2025 to 2035
- Global Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Device Type
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Device Type , 2020 to 2024
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Device Type , 2025 to 2035
- Laptop
- Tablet
- Smartphone
- Y-o-Y Growth Trend Analysis By Device Type , 2020 to 2024
- Absolute $ Opportunity Analysis By Device Type , 2025 to 2035
- Global Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Solution Type
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Solution Type, 2020 to 2024
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Solution Type, 2025 to 2035
- Mobile Data Security
- Mobile Device Security
- Network Security
- Y-o-Y Growth Trend Analysis By Solution Type, 2020 to 2024
- Absolute $ Opportunity Analysis By Solution Type, 2025 to 2035
- Global Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Region
- Introduction
- Historical Market Size Value (USD Million) Analysis By Region, 2020 to 2024
- Current Market Size Value (USD Million) Analysis and Forecast By Region, 2025 to 2035
- North America
- Latin America
- Western Europe
- Eastern Europe
- East Asia
- South Asia and Pacific
- Middle East & Africa
- Market Attractiveness Analysis By Region
- North America Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- USA
- Canada
- Mexico
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- Latin America Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- Brazil
- Chile
- Rest of Latin America
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- Western Europe Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- Germany
- UK
- Italy
- Spain
- France
- Nordic
- BENELUX
- Rest of Western Europe
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- Eastern Europe Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- Russia
- Poland
- Hungary
- Balkan & Baltic
- Rest of Eastern Europe
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- East Asia Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- China
- Japan
- South Korea
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- South Asia and Pacific Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- India
- ASEAN
- Australia & New Zealand
- Rest of South Asia and Pacific
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- Middle East & Africa Market Analysis 2020 to 2024 and Forecast 2025 to 2035, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2020 to 2024
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2025 to 2035
- By Country
- Kingdom of Saudi Arabia
- Other GCC Countries
- Turkiye
- South Africa
- Other African Union
- Rest of Middle East & Africa
- By Device Type
- By Solution Type
- By Country
- Market Attractiveness Analysis
- By Country
- By Device Type
- By Solution Type
- Key Takeaways
- Key Countries Market Analysis
- USA
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Canada
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Mexico
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Brazil
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Chile
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Germany
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- UK
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Italy
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Spain
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- France
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- India
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- ASEAN
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Australia & New Zealand
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- China
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Japan
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- South Korea
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Russia
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Poland
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Hungary
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Kingdom of Saudi Arabia
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- Turkiye
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- South Africa
- Pricing Analysis
- Market Share Analysis, 2024
- By Device Type
- By Solution Type
- USA
- Market Structure Analysis
- Competition Dashboard
- Competition Benchmarking
- Market Share Analysis of Top Players
- By Regional
- By Device Type
- By Solution Type
- Competition Analysis
- Competition Deep Dive
- IBM
- Overview
- Product Portfolio
- Profitability by Market Segments (Product/Age /Sales Channel/Region)
- Sales Footprint
- Strategy Overview
- Marketing Strategy
- Product Strategy
- Channel Strategy
- Quokka
- Palo Alto Networks
- Qualcomm
- Zimperium
- NIST
- Intel
- Lenovo
- IBM
- Competition Deep Dive
- Assumptions & Acronyms Used
- Research Methodology
List of Tables
- Table 1: Global Market Value (USD Million) Forecast by Region, 2020-2035
- Table 2: Global Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 3: Global Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 4: North America Market Value (USD Million) Forecast by Country, 2020-2035
- Table 5: North America Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 6: North America Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 7: Latin America Market Value (USD Million) Forecast by Country, 2020-2035
- Table 8: Latin America Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 9: Latin America Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 10: Western Europe Market Value (USD Million) Forecast by Country, 2020-2035
- Table 11: Western Europe Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 12: Western Europe Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 13: Eastern Europe Market Value (USD Million) Forecast by Country, 2020-2035
- Table 14: Eastern Europe Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 15: Eastern Europe Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 16: East Asia Market Value (USD Million) Forecast by Country, 2020-2035
- Table 17: East Asia Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 18: East Asia Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 19: South Asia and Pacific Market Value (USD Million) Forecast by Country, 2020-2035
- Table 20: South Asia and Pacific Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 21: South Asia and Pacific Market Value (USD Million) Forecast by Solution Type, 2020-2035
- Table 22: Middle East & Africa Market Value (USD Million) Forecast by Country, 2020-2035
- Table 23: Middle East & Africa Market Value (USD Million) Forecast by Device Type , 2020-2035
- Table 24: Middle East & Africa Market Value (USD Million) Forecast by Solution Type, 2020-2035
List of Figures
- Figure 1: Global Market Pricing Analysis
- Figure 2: Global Market Value (USD Million) Forecast 2020-2035
- Figure 3: Global Market Value (USD Million) Share and BPS Analysis by Region, 2025 and 2035
- Figure 4: Global Market Y-o-Y Growth Comparison by Region, 2025-2035
- Figure 5: Global Market Attractiveness Analysis by Region
- Figure 6: North America Market Incremental Dollar Opportunity, 2025-2035
- Figure 7: Latin America Market Incremental Dollar Opportunity, 2025-2035
- Figure 8: Western Europe Market Incremental Dollar Opportunity, 2025-2035
- Figure 9: Eastern Europe Market Incremental Dollar Opportunity, 2025-2035
- Figure 10: East Asia Market Incremental Dollar Opportunity, 2025-2035
- Figure 11: South Asia and Pacific Market Incremental Dollar Opportunity, 2025-2035
- Figure 12: Middle East & Africa Market Incremental Dollar Opportunity, 2025-2035
- Figure 13: North America Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 14: Latin America Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 15: Western Europe Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 16: Eastern Europe Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 17: East Asia Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 18: South Asia and Pacific Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 19: Middle East & Africa Market Value Share and BPS Analysis by Country, 2025 and 2035
- Figure 20: Global Market - Tier Structure Analysis
- Figure 21: Global Market - Company Share Analysis