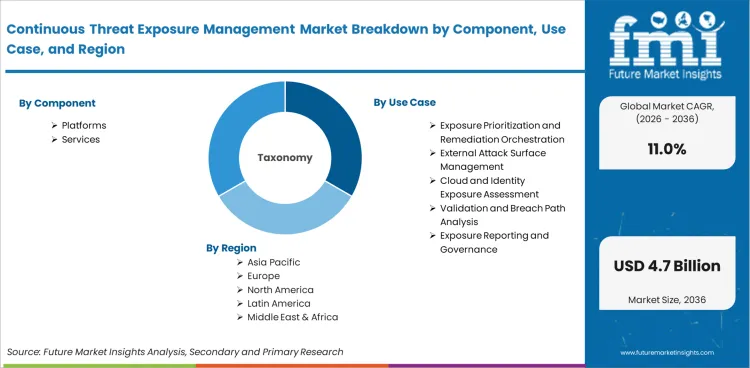
The continuous threat exposure management market was valued at an estimated USD 1.34 billion in 2025, is projected to reach USD 1.48 billion in 2026, and is forecast to expand to USD 4.22 billion by 2036 at a CAGR of 11.0%. Demand is being reshaped by the rise in vulnerability exploitation, growth in external and cloud attack surfaces, and stronger customer preference for unified exposure workflows rather than fragmented point tools.
| Parameter | Details |
|---|---|
| Market value (2026) | USD 1.48 billion |
| Forecast value (2036) | USD 4.22 billion |
| CAGR (2026 to 2036) | 11.0% |
| Estimated market value (2025) | USD 1.34 billion |
| Incremental opportunity | USD 2.74 billion |
| Leading component | Platforms, 58.6% of component revenue |
| Leading use case | Exposure prioritization and remediation orchestration, 31.8% of use-case revenue |
| Leading enterprise size | Large enterprises, 69.4% of enterprise-size revenue |
| Key players | Tenable, Rapid7, Qualys, Palo Alto Networks, XM Cyber, Armis |
Source: Analyst synthesis from authoritative sources, 2026.

The market is being shaped by higher exploitation pressure, a growing body of known exploited vulnerabilities, and broader vendor expansion into exposure-management platforms. Verizon reported a 34% rise in vulnerability exploitation as an initial access vector in the 2025 DBIR, CISA continues to expand the Known Exploited Vulnerabilities catalog, and major cybersecurity vendors are combining visibility, context, and remediation workflows in broader exposure platforms.
Across tracked geographies, India sets the pace at 13.2% CAGR. Singapore follows at 12.8%. United States follows at 10.8%. United Kingdom follows at 10.4%. Germany follows at 10.1%. Japan follows at 9.4%.
The continuous threat exposure management market covers software platforms and related services used to continuously discover, assess, validate, prioritize, and drive remediation of exploitable cyber exposures across hybrid environments. The market includes products that unify exposure data from attack surface management, asset context, vulnerability intelligence, security validation, and remediation workflows into an ongoing risk-reduction process.
Market scope includes exposure management platforms, external attack surface management modules, asset-context layers, risk-prioritization engines, security validation and simulation components used inside CTEM workflows, and related implementation and advisory services. Revenue sizing spans subscriptions and services used to identify exploitable paths across cloud, endpoint, identity, application, and network environments.
The scope excludes stand-alone legacy vulnerability scanners without continuous exposure workflow capability, generic SIEM and SOAR revenue not directly tied to CTEM offerings, managed detection and response services, and broad consulting work not attached to continuous exposure management products or deployments.
Organizations are no longer struggling with asset visibility alone. They are struggling with overload in findings, fragmented ownership, and slow remediation across cloud, identity, endpoint, and third-party exposure points.
Threat pressure is making prioritization more urgent. Verizon's 2025 DBIR showed stronger use of vulnerabilities in breach entry, and CISA's KEV process keeps reinforcing the gap between raw vulnerability counts and actively dangerous exposure.
Vendor strategy has shifted toward platformization. Public cybersecurity vendors are increasingly bundling attack surface management, contextual risk scoring, validation, and remediation guidance into one workflow.
The market is growing because security teams no longer get enough value from isolated scanners or dashboards. CTEM programs aim to connect discovery, exploitability, business criticality, and action in one loop. That is a stronger budget narrative than visibility alone because it links directly to measurable risk reduction.
Cloud sprawl, unmanaged assets, exposed identities, and software supply-chain complexity have widened the exposure problem. Traditional vulnerability management remains necessary, but it does not always tell teams which findings matter now. CTEM tools are gaining traction because they organize security work around reachable and consequential exposure rather than raw volume.
This shift is visible in vendor portfolios. Tenable markets exposure management across cloud, identity, and operational technology. Rapid7 has expanded into exposure command and attack-surface workflows. Palo Alto Networks continues to link cloud and attack-surface data inside broader platform operations. As platform vendors normalize this category, buyer confidence rises.
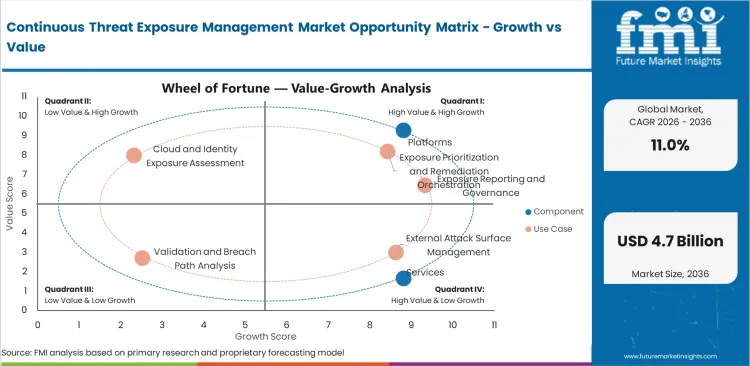
The market is segmented by component, deployment model, use case, enterprise size, end use, and region. By component, the market includes platforms and services. By use case, it covers exposure prioritization and remediation orchestration, external attack surface management, cloud and identity exposure assessment, validation and breach path analysis, and board-level exposure reporting.
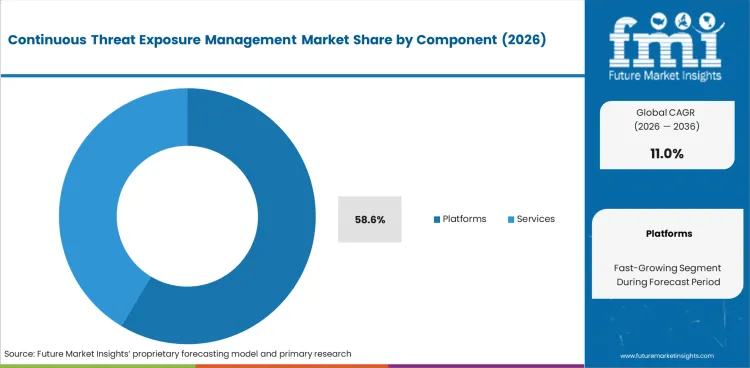
Platforms are projected to hold 58.6% of component revenue in 2026. This lead reflects enterprise demand for fewer workflow handoffs, stronger contextual scoring, and easier executive reporting. Platform vendors can also bundle adjacent capabilities more effectively than services-led providers.
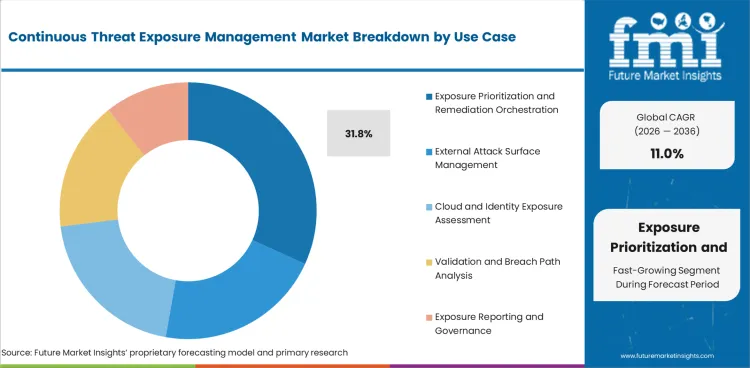
Exposure prioritization and remediation orchestration is expected to capture 31.8% of use-case revenue in 2026. This segment leads because security teams need defensible reduction of exploitability, ticket load, and time-to-remediation. Products that rank reachable or high-impact exposures and connect them to action can justify larger budget share.
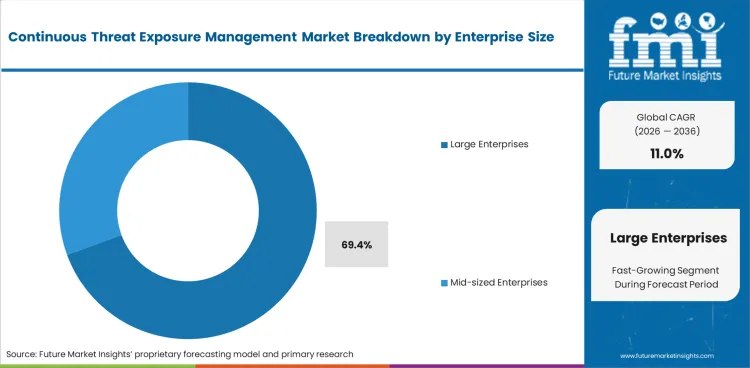
Large enterprises are projected to account for 69.4% of enterprise-size revenue in 2026. They are earlier adopters because they run broad cloud estates, large identity environments, and global remediation workflows that make exposure management economically meaningful at scale.
Driver: rising exploitation of known exposures is pushing security teams toward risk-based prioritization and continuous validation.
Restraint: data integration complexity and workflow ownership across IT, cloud, security, and engineering still slow program rollout.
Trend: cybersecurity platforms are converging around exposure-management workflows that combine attack-surface visibility, context, and action.
Adoption rates differ by security maturity. Organizations with strong asset data, executive sponsorship, and established remediation processes move faster. Teams with weak ownership, poor CMDB quality, or fragmented cloud inventories take longer to realize value.
Growth is supported by the shift from vulnerability counting to exploitability-driven action. Official exploitation and KEV data make it easier for CISOs to justify CTEM investment because the category answers a practical question: which exposures are most likely to lead to damage now.
Operational complexity remains a core market constraint. CTEM depends on clean asset context, cross-team ownership, ticketing alignment, and confidence in remediation logic. Organizations that cannot connect discovery data with business context and accountable owners will underuse platform capabilities.
Platform convergence is becoming a defining feature of this market. Exposure management is being absorbed into broader security platforms, especially where vendors already own vulnerability management, cloud security, asset visibility, or SOC workflows. This is increasing competition and widening buyer familiarity with the category.
.webp)
North America remains the largest revenue base because platform budgets are deep, enterprise cloud exposure is broad, and public cybersecurity vendors are concentrated there.
Asia grows faster because digital infrastructure is scaling quickly and newer enterprises are more willing to adopt platform-led security operations without as much legacy tooling drag.
Europe grows steadily on the strength of regulatory pressure, cloud-security spending, and greater board focus on cyber resilience, though rollout speed varies by country and enterprise maturity.
| Country | CAGR |
|---|---|
| India | 13.2% |
| Singapore | 12.8% |
| United States | 10.8% |
| United Kingdom | 10.4% |
| Germany | 10.1% |
| Japan | 9.4% |
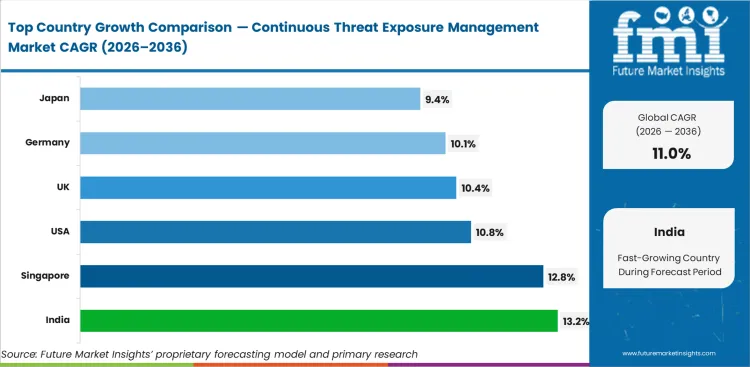
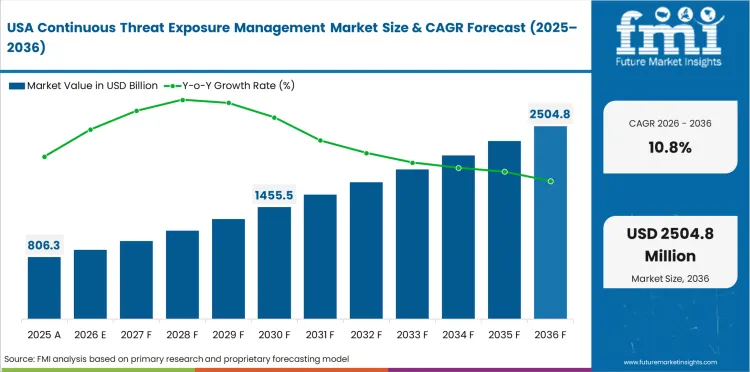
The United States is projected to grow at a CAGR of 10.8% through 2036. Growth is supported by a strong cybersecurity software base, faster platform consolidation, and earlier enterprise adoption of exposure-management workflows.
The United Kingdom is projected to grow at a CAGR of 10.4% through 2036. Adoption is supported by mature enterprise cybersecurity demand and strong interest in measurable cyber-risk reduction.
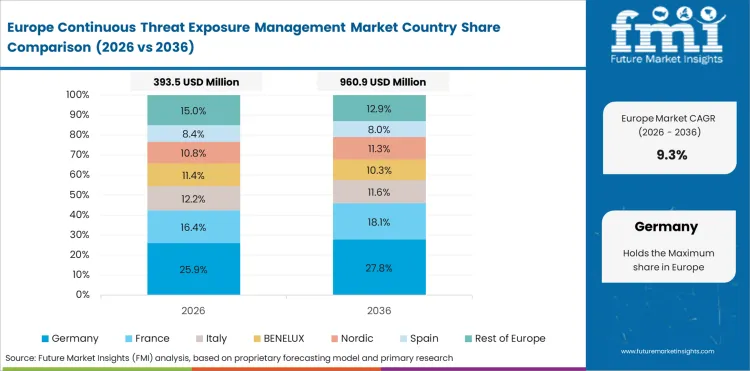
Germany is expected to grow at a CAGR of 10.1% through 2036. Industrial and enterprise cloud adoption creates exposure-management demand, though implementation quality remains critical.
Japan is projected to grow at a CAGR of 9.4% through 2036. Demand is improving as enterprises modernize cloud and identity architectures, but program rollout tends to be measured.
India is projected to grow at a CAGR of 13.2% through 2036. Growth is driven by rapid digital expansion, cloud adoption, and strong enterprise need to rationalize growing exposure across modern environments.
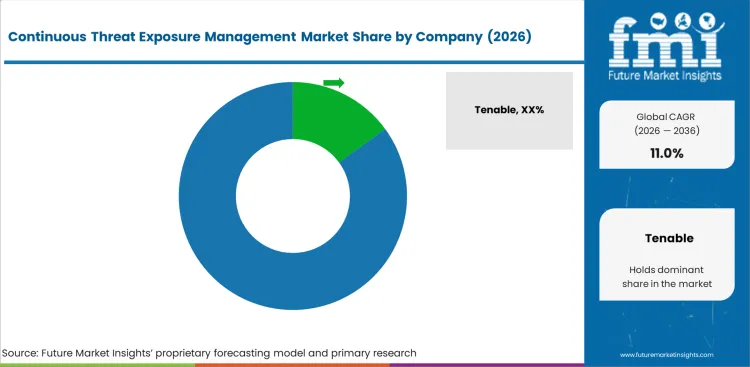
The competitive landscape is led by cybersecurity vendors that already own adjacent control points such as vulnerability management, attack surface management, cloud security, exposure analytics, and remediation workflows. Category leadership depends on data breadth, contextual prioritization, workflow depth, and cross-domain integration.
Tenable, Rapid7, Qualys, and Palo Alto Networks are among the most visible large-platform competitors. Their advantage comes from installed base, channel reach, and the ability to cross-sell exposure management into existing security programs.
XM Cyber and Armis hold differentiated positions through attack-path analysis and broad cyber asset context. These players benefit when buyers want outcome-oriented exposure mapping rather than scanner-led workflows alone.
The market remains open enough for specialized firms to win, but platform breadth is becoming more important as enterprises seek fewer consoles and clearer remediation ownership.
Major Industry Players
Tenable and Rapid7 are strong because they can connect vulnerability, asset, and external exposure workflows inside established security operations accounts. Qualys remains relevant through large enterprise coverage and an established cloud delivery model.
Palo Alto Networks brings broader platform strength and can attach exposure-management workflows to cloud and SOC programs. That gives it leverage in large enterprise consolidation cycles.
XM Cyber and Armis remain important in accounts where attack-path analysis, asset context, and business-impact narrative are central to the buying decision.
| Company | Exposure Data Breadth | Prioritization Depth | Workflow Integration | Geographic Reach |
|---|---|---|---|---|
| Tenable | High | High | High | Strong |
| Rapid7 | High | High | High | Strong |
| Qualys | High | Medium | High | Strong |
| Palo Alto Networks | High | High | High | Strong |
| XM Cyber | Medium | High | Medium | Moderate |
| Armis | High | Medium | Medium | Strong |
Source: Analyst synthesis from authoritative sources, 2026. Ratings reflect relative positioning based on disclosed capabilities and market presence.
Key Developments in Continuous Threat Exposure Management Market
Major Global Players:
Emerging Players/Startups
| Metric | Values |
|---|---|
| Quantitative Units | USD 1.48 billion to USD 4.22 billion, at a CAGR of 11.0% |
| Market Definition | Software platforms and related services used to continuously discover, assess, validate, prioritize, and drive remediation of cyber exposures across hybrid environments. |
| Segmentation | Component: platforms, services. Deployment: cloud, hybrid. Use case: exposure prioritization and remediation orchestration, external attack surface management, cloud and identity exposure assessment, validation and breach path analysis, exposure reporting. Enterprise size: large enterprises, mid-sized enterprises. End use: BFSI, technology and telecom, government and defense, healthcare, industrial and manufacturing, retail and e-commerce. Region: North America, Europe, Asia Pacific, Latin America, Middle East and Africa. |
| Regions Covered | North America, Europe, Asia Pacific, Latin America, Middle East and Africa |
| Countries Covered | United States, United Kingdom, Germany, Japan, India, Singapore and others |
| Key Companies Profiled | Tenable, Rapid7, Qualys, Palo Alto Networks, XM Cyber, Armis |
| Forecast Period | 2026 to 2036 |
| Approach | Analyst-built hybrid top-down and bottom-up model using official exploitation data, vendor positioning, and platform expansion disclosures. |
| Historical Period | 2020 to 2025 |
How large is the demand for Continuous Threat Exposure Management in the global market in 2026?
Demand for continuous threat exposure management in the global market is estimated at USD 1.48 billion in 2026.
What will be the market size by 2036?
Market size is projected to reach USD 4.22 billion by 2036.
What is the expected demand growth between 2026 and 2036?
Demand is expected to grow at a CAGR of 11.0% between 2026 and 2036.
Which component is poised to lead by 2026?
Platforms lead the market in 2026 with 58.6% of component revenue.
How are large enterprises driving adoption?
Large enterprises account for 69.4% of enterprise-size revenue because they face broader hybrid attack surfaces and have stronger platform consolidation budgets.
What is driving demand in the United States?
The United States is projected to grow at a CAGR of 10.8% through 2036, supported by high cybersecurity software spending, platform consolidation, and earlier adoption of exposure-management workflows.
What does the market definition mean?
The market covers software platforms and related services used to continuously discover, assess, validate, prioritize, and drive remediation of cyber exposures across hybrid environments.
How does the analyst validate the forecast?
The forecast is validated through a hybrid model using official exploitation data, vendor platform expansion, and bottom-up checks on adjacent exposure-management budgets and product overlap.
Full Research Suite comprises of:
Market outlook & trends analysis
Interviews & case studies
Strategic recommendations
Vendor profiles & capabilities analysis
5-year forecasts
8 regions and 60+ country-level data splits
Market segment data splits
12 months of continuous data updates
DELIVERED AS:
PDF EXCEL ONLINE
Thank you!
You will receive an email from our Business Development Manager. Please be sure to check your SPAM/JUNK folder too.