Wearable Medical Device Connectivity and Cybersecurity Test Systems Market
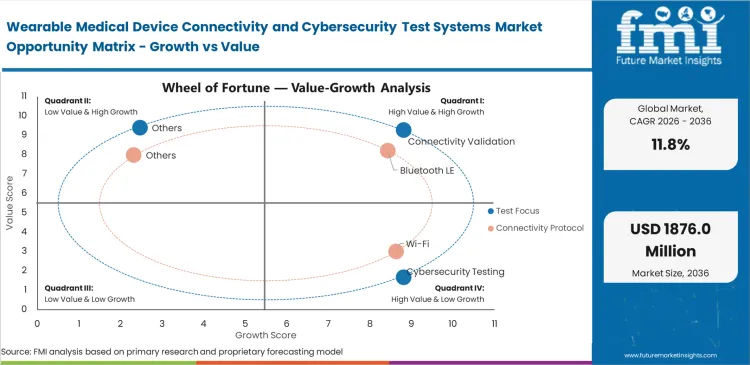
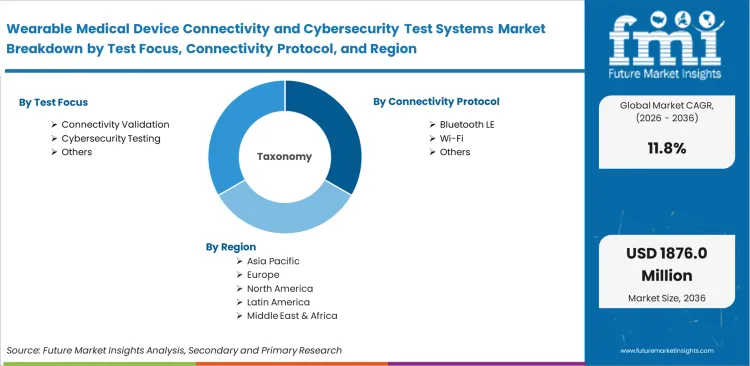
The Wearable Medical Device Connectivity And Cybersecurity Test Systems Market Is Segmented By Test Focus (Connectivity Validation, Cybersecurity Testing, Interoperability Testing, Performance Verification, Compliance Documentation), Connectivity Protocol (Bluetooth LE, Wi-Fi, Cellular, NFC, UWB), Deployment Mode (Lab Systems, Cloud Platforms, Hybrid Systems, Embedded Tools, Portable Kits), End User (OEMs, Test Labs, Hospitals, Design Firms, CROs), Wearable Class (Monitoring Patches, Smartwatches, CGM Wearables, Cardiac Wearables, Therapy Wearables), And Region. Forecast For 2026 To 2036.
Historical Data Covered: 2016 to 2024 | Base Year: 2025 | Estimated Year: 2026 | Forecast Period: 2027 to 2036
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Size, Market Forecast and Outlook By FMI
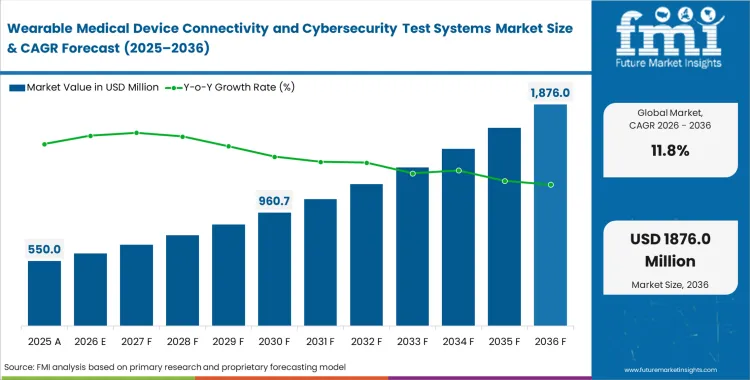
The wearable medical device connectivity and cybersecurity test systems market surpassed a value of USD 490 million in 2025. Sales are expected to surpass USD 550 million in 2026 at a CAGR of 11.8% during the forecast period. Steady investment shapes the industry forecast, lifting total valuation to USD 1,680 million through 2036 as regulatory bodies mandate continuous vulnerability scanning for all devices with bidirectional data flow.
Summary of Wearable Medical Device Connectivity and Cybersecurity Test Systems Market
- Market Snapshot
- The market for wearable medical device connectivity and cybersecurity test systems market is valued at USD 490 million in 2025 and is expected to grow to USD 1,680 million by 2036.
- Experts predict this space expected to grow at a 11.8% CAGR between 2026 and 2036, adding a massive USD 1,130 million in fresh revenue along the way.
- Success in this highly regulated testing space relies on proving a device's wireless strength, gathering hard evidence of its cyber defenses, ensuring it works well with other hospital systems, and keeping flawless paperwork.
- Driving this demand are strict FDA rules on how devices connect and protect data, alongside the massive shift toward sending patients home with digital health sensors attached to their bodies.
- Demand and Growth Drivers
- Sales are climbing because wearable medical gear must prove it can safely send data, pair with phones, and link up with hospital networks in real-life situations, not just in a quiet laboratory.
- Hacking prevention has become a massive priority since new FDA rules force manufacturers to submit detailed proof of their cyber defenses before a device can even go to market.
- Making sure different wireless signals do not block each other is absolutely critical now that Bluetooth and Wi-Fi are heavily used to monitor patients resting at home.
- Looking across the globe, China is projected to lead the pack with an estimated 13.4% CAGR. Other major testing hubs include India as anticipated to scale at a 12.9% CAGR, Germany at 11.6%, the United Kingdom at 10.9%, the United States at 10.8%, South Korea at 10.5%, and Japan likely to grow at a 10.1% CAGR.
- A few hurdles slow things down, like the massive expense of building complex testing labs, the long time it takes to check every feature, and the constant need to update security tests long after a product is sold.
- Product and Segment View
- The equipment sold here ranges from physical tabletop testing rigs and wireless signal checkers to software that hunts for cyber flaws and organizes compliance paperwork across Bluetooth LE, Wi-Fi, cellular, and NFC connections.
- Engineers use these tools to validate everything from continuous glucose monitors and heart-tracking smartwatches to sticky health patches that beam patient vitals straight to hospital servers.
- Making sure the signal actually stays connected is the top priority, which is why connectivity validation is estimated to capture a massive 34.0% share of the test focus segment. If a wearable drops its connection to the cloud, its physical design does not matter at all.
- When looking at how devices talk to each other, Bluetooth LE is anticipated to dominate the connectivity protocol segment with a 39.0% share. This dominance comes from the simple fact that small, body-worn monitors need to share data constantly without draining their tiny batteries.
- A solid 46.0% share is predicted to go to lab systems within the deployment mode category. Regulators still demand that device makers prove their safety claims using heavily controlled and tightly documented physical environments.
- Projecting original equipment manufacturers (OEMs) to stand out as the biggest buyers, leading an expected 41.0% share of the end user segment. This makes sense because companies must spend heavily to pass security checks long before they are allowed to sell their devices.
- Monitoring patches are estimated to account for a 31.0% share of the wearable class segment. Their popularity is surging as doctors increasingly rely on these stick-on sensors to watch over patients recovering at home.
- This testing space specifically covers tools that check the wireless strength and hacking resistance of medical gear worn on the outside of the body. It does not include testing for devices implanted inside patients, basic consumer fitness trackers, or general hospital IT security.
- Geography and Competitive Outlook
- China, India, and Germany are sprinting ahead as the fastest-growing regions for this equipment. The United States remains the biggest and most valuable buyer because of its massive tech innovation, strict FDA rules, and deeply established testing labs.
- To win contracts today, testing suppliers cannot just sell one piece of equipment. They have to offer all-in-one systems that handle radio signal checks, cyber defense, and network compatibility at the exact same time.
- Major companies providing these solutions include UL Solutions, Intertek, SGS, TÜV SÜD, DEKRA, Keysight Technologies, and Rohde & Schwarz. Their success hinges on having recognized safety accreditations and operating testing labs all over the world.
- The market is still incredibly spread out. This fragmentation happens because device makers typically hire different specialists to handle their radio tests, software hacks, and final certification paperwork.
Compliance teams have less time than ever to check software updates before new wearable medical device FDA cybersecurity requirements take effect. Missing these testing deadlines directly stops a new product from hitting the market. To speed things up, product managers building wearable medical devices now insist on running wireless coexistence testing for medical wearables all at the same time, rather than checking one radio signal after another. Simply turning a monitor on to see if it tracks a heartbeat is no longer enough. Basic checks completely miss the hidden risks that emerge the second wearable healthcare devices log into a vulnerable hospital Wi-Fi system.
Hospitals are locking down their buying habits, adopting strict rules where no outside device is automatically trusted on their servers. To even get into a hospital's product catalog, manufacturers have to prove their data stays securely scrambled by surviving intense wearable medical device penetration testing. Hospital security directors are driving this massive shift on the ground. They actively refuse to buy older patient monitoring devices or skin patches if the device maker cannot provide a clear list of every software ingredient inside the machine or prove exactly how it securely connects to the network.
Demand for testing infrastructure in China is anticipated to rise at a CAGR of 13.4% through 2036, driven by aggressive domestic medical IoT standardization. India is likely to track at a CAGR of 12.9% as contract manufacturing expands outsourced testing capacity. Germany is anticipated to records a CAGR of 11.6%, followed by the United Kingdom expected to grow at 10.9% and the United States to be projected at 10.8%. South Korea and Japan are likely to register CAGRs of 10.5% and 10.1%, respectively. Compliance parameters fragment across regional lines based on strict data localization laws.
Segmental Analysis
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis by Test Focus
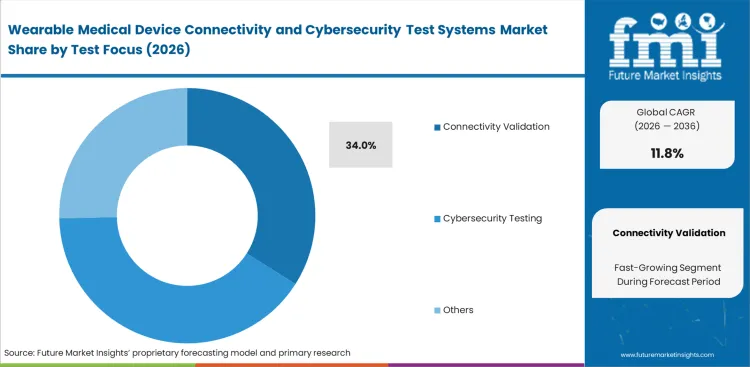
Regulatory compliance officers rely on clear evidence that wireless sensors maintain connections under clinical interference before they even consider encryption strength. The connectivity validation segment is estimated to account for 34.0% share in 2026 within the broader wearable medical device connectivity testing market. Based on FMI's assessment, remote patient monitoring system architectures dictate this priority because a dropped signal during cardiac monitoring poses an immediate physical risk, whereas a data breach represents a delayed informational risk. Product engineers spend the majority of their validation budget ensuring that a wearable patch can jump between hospital Wi-Fi and cellular networks without dropping data packets. As manufacturers rarely advertise that their most expensive cybersecurity simulators are frequently used just to verify basic Bluetooth pairing stability across different smartphone operating systems. The companies that delay investing in automated RF coexistence testing face compounding product launch delays as manual testing proves insufficient for modern regulatory submissions.
- Pre-Market Qualification: Design engineers run continuous signal integrity simulations to identify antenna dead zones. Product managers gain the data necessary to guarantee uptime specifications to clinical buyers.
- Interference Simulation: Clinical environments host dozens of competing radio frequencies that choke standard connections. Quality assurance teams avoid post-launch recalls by recreating these dense RF conditions during the prototyping phase.
- Lifecycle Maintenance: Firmware updates frequently alter how a device handles wireless handshakes. Software developers must perform regression testing to ensure security patches do not break existing connectivity functions.
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis by Connectivity Protocol
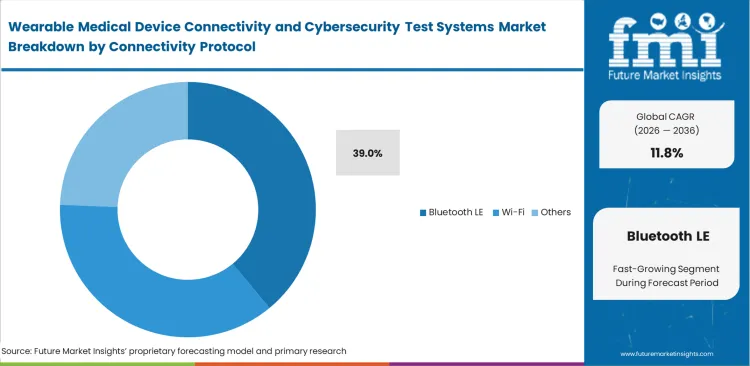
Low-power sensors dictate protocol choices for continuous physiological tracking. FMI analysts point out that power constraints force design firms to abandon high-bandwidth protocols, elevating the necessity of Bluetooth LE testing for wearable medical devices. Hardware engineers build remote home monitoring systems around this standard because patients universally own smartphones capable of acting as secure data relays. The reliance on consumer smartphones introduces a massive attack surface, forcing test labs to simulate hundreds of unpatched mobile operating systems to verify secure data handovers. What procurement directors miss during equipment selection is that testing a Bluetooth medical device requires validating the security of the commercial phone it pairs with, not just the medical sensor itself. The Bluetooth LE category is expected to hold 39.0% share in 2026, as companies relying on older testing rigs struggle to capture the complex frequency-hopping algorithms used in the latest low-energy specifications.
- Energy-Budget Constraints: Battery size strictly limits transmission power in skin-adherent patches. Hardware architects face strict trade-offs between continuous encryption processing and device battery life.
- Mobile Relay Vulnerabilities: Medical patches dump data to consumer phones rather than direct clinical servers. Security analysts must validate the encrypted tunnel between the wearable and the patient's personal device.
- Protocol Evolution: Standards bodies continuously release updated security specifications for short-range wireless. Certification engineers must constantly upgrade testing software to verify compliance with the latest encryption keys.
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis by Deployment Mode
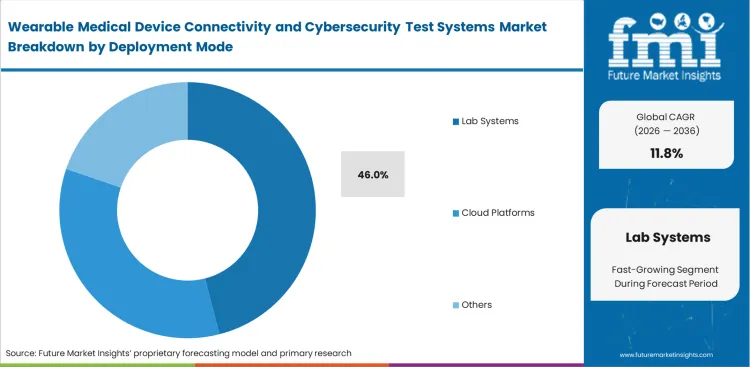
Repeatable RF environments are functionally impossible to guarantee in open office settings or clinical wards. The lab systems segment is poised to garner 46.0% share in 2026, as FMI observes that regulatory bodies reject remote healthcare test data unless it is generated inside a dedicated interoperability testing lab for medical wearables that eliminates external background noise. Compliance directors at medical OEMs mandate the use of physical anechoic chambers to measure precise antenna radiation patterns. Cloud-based simulation tools handle software vulnerability scanning, but validating physical radio hardware still requires heavy, localized test racks inside a cybersecurity compliance lab for FDA wearable device submission. The irony of testing highly mobile patient wearables is that the certification process relies entirely on massive, stationary laboratory infrastructure that cannot be moved. Startups attempting to shortcut physical lab validation using software models inevitably face FDA rejection when physical device behavior deviates from digital projections.
- Baseline RF Isolation: Ambient cellular and Wi-Fi signals ruin sensitive medical transmission measurements. Hardware testers require heavy shielding enclosures to isolate the specific frequency under evaluation.
- Automated Physical Rotation: Antenna performance changes depending on the physical orientation of the patient's body. Lab technicians use automated positioning systems to map signal strength across three dimensions.
- Audit Trail Generation: Regulatory submissions demand exact records of the physical testing environment. Quality managers rely on integrated lab software to automatically stamp reports with calibration data.
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis by End User
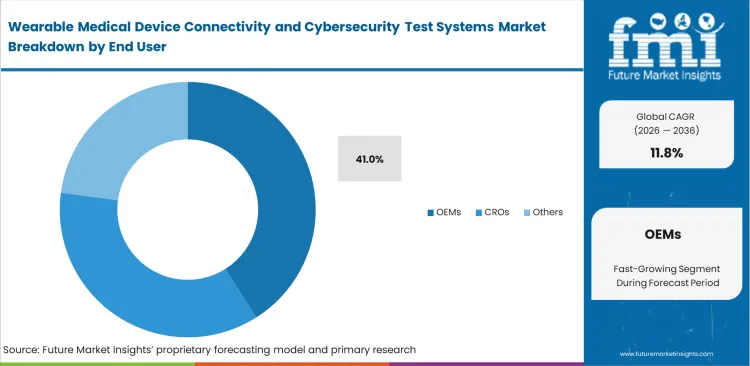
Internalizing security validation shortens product development cycles compared to waiting in queues at third-party certification houses. In FMI's view, development speeds for digital healthcare software move too fast for outsourced testing models, explaining why the OEMs are anticipated to capture 41.0% of the market in 2026. Software engineering leads require immediate feedback on how a new line of code impacts protocol security. Buying dedicated test equipment allows internal teams to run automated vulnerability scans overnight rather than booking expensive hourly blocks at external facilities. Independent wearable medical device testing suppliers actually encourage this trend, preferring OEMs to conduct basic debugging internally so the labs can focus on high-margin, final regulatory sign-offs. Device manufacturers lacking internal testing capacity routinely miss commercial launch windows because they discover fundamental security flaws only during final external audits.
- Agile Development Loops: Software teams push firmware updates weekly to patch newly discovered cyber threats. Quality engineers require internal testing racks to validate these patches instantly.
- Pre-Compliance Screening: Failing an official certification test requires costly redesigns and re-bookings. Compliance directors avoid these penalties by running identical test suites internally before formal submission.
- Post-Market Surveillance: Connected devices face new cyber threats long after they leave the factory. Security operations centers inside large OEMs must constantly test existing devices against newly published vulnerabilities.
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis by Wearable Class
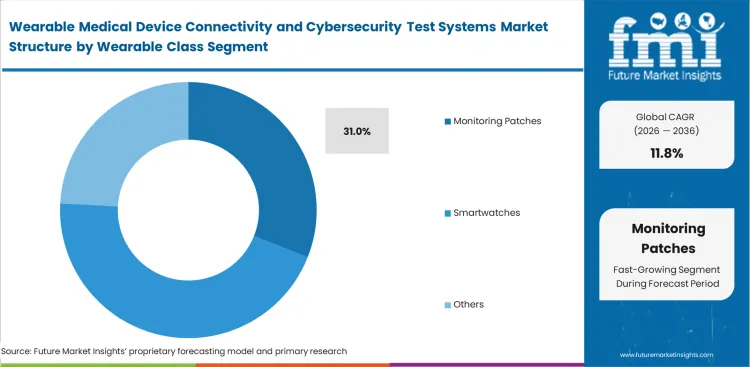
Clinical-grade data collection is migrating from bulky bedside monitors to discreet, disposable body sensors. According to FMI's estimates, these disposable form factors present the hardest validation challenges for global digital health engineers executing smart patch wireless validation. Formulators embedding tiny antennas into flexible medical adhesives struggle to maintain signal integrity as the patient moves and the patch bends. The hardware is meant to be cheap and disposable, yet it must meet the exact same cryptographic standards as a ten-thousand-dollar hospital monitor, resulting in the monitoring patches segment forecast to command a 31.0% share in 2026. The factor that generalist engineers fail to realize is that human sweat actively degrades the RF performance of skin-contact antennas, requiring test labs to simulate bodily fluids during connectivity validation. Patches that pass pristine lab tests frequently fail in actual clinical trials when physical wear alters the antenna geometry.
- Flexible Antenna Physics: Bending a wearable patch physically changes its radio transmission characteristics. Hardware engineers must test the device under mechanical stress to ensure the connection survives patient movement.
- Fluid Interference: Human skin and sweat absorb specific radio frequencies. RF technicians use specialized phantom materials that mimic human tissue properties to accurately measure signal degradation.
- Disposable Economics: The electronics inside a patch must be cheap enough to discard after a few days. Component buyers face immense pressure to select inexpensive wireless chips that still pass rigorous security testing.
Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Drivers, Restraints, and Opportunities
Government rules now require device makers to track and document cybersecurity risks from the moment a product is built until it retires. Security directors at manufacturing firms are blocked from selling their telehealth and telemedicine products if they fail to prove the devices stop known hacks, a strict requirement under the latest wearable device interoperability FDA guidance. Health agencies no longer accept a single security test passed on launch day. Device builders must constantly test against new cyber threats and check every software update they send out over the air. This constant cycle forces companies to buy automated testing stations that can run these checks around the clock without human help.
Trying to force different testing methods into one clean report creates massive headaches for engineering teams when they compare interoperability testing and cybersecurity testing in medical wearables. Lab managers run into trouble because checking the physical radio signals and trying to hack the software usually require completely different machines and computer programs. Mixing physical radio checks with encryption tests slows down the whole approval process. The numbers coming out of a radio frequency scanner almost never line up cleanly with the error logs from a software hacking tool. As the systems do not talk to each other, companies end up pasting their testing data together by hand, which results with mistakes and pushes back the launch date.
- Automated Fuzzing Integration: Software engineers lack tools that seamlessly inject malformed data packets over actual RF connections. Developing hybrid testers that combine physical next generation telehealth radio links with software vulnerability scanners accelerates development.
- Cloud-Based Validation Environments: Smaller design firms cannot afford massive anechoic chambers. Offering remote access to physical test rigs allows startups to validate designs without intense capital expenditure.
- Simulated Hospital RF Conditions: Quality assurance teams need realistic clinical interference models. Selling standardized software profiles that mimic the exact RF noise of a busy intensive care unit improves testing accuracy.
Regional Analysis
Examining the global map reveals that regional testing requirements are fracturing, as local governments impose their own strict data rules on medical wearable. Based on regional analysis, the market is segmented into North America, Europe, and East Asia across 40 plus countries.
.webp)
| Country | CAGR (2026 to 2036) |
|---|---|
| China | 13.4% |
| India | 12.9% |
| Germany | 11.6% |
| United Kingdom | 10.9% |
| United States | 10.8% |
| South Korea | 10.5% |
| Japan | 10.1% |
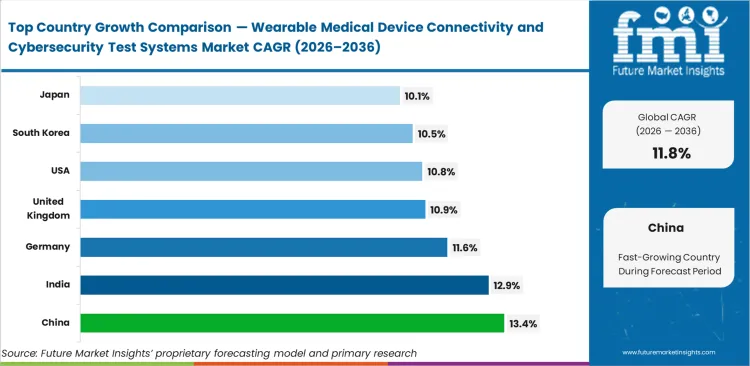
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
North America Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis
Stringent FDA premarket cybersecurity guidance forces manufacturers to expand internal validation capabilities drastically. Compliance directors across North America allocate massive capital specifically to avoid regulatory rejection during the 510(k)-submission process. FMI analysts point out that the rapid adoption of telehealth software expands the attack surface for clinical data, prompting hospital networks to demand third-party penetration testing certificates before procurement. The regional dynamic shifts as OEMs realize that testing early in the design phase is cheaper than patching vulnerabilities post-launch.
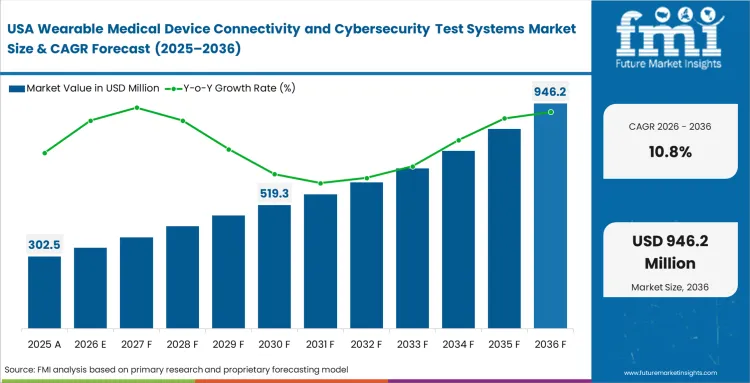
- United States: Demand across the United States wearable medical device testing market is anticipated to rise at a CAGR of 10.8% through 2036. Security architects prioritize automated fuzzing tools to meet strict federal guidelines for medical IoT. OEMs that master automated compliance reporting lock in lucrative hospital contracts by demonstrating superior data protection.
FMI's report includes additional North American countries like Canada, where similar regulatory pressures apply. In the end, the ability to generate verifiable radio frequency and cybersecurity audit trails internally is becoming the main competitive advantage for medical hardware developers operating in this region.
Europe Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis
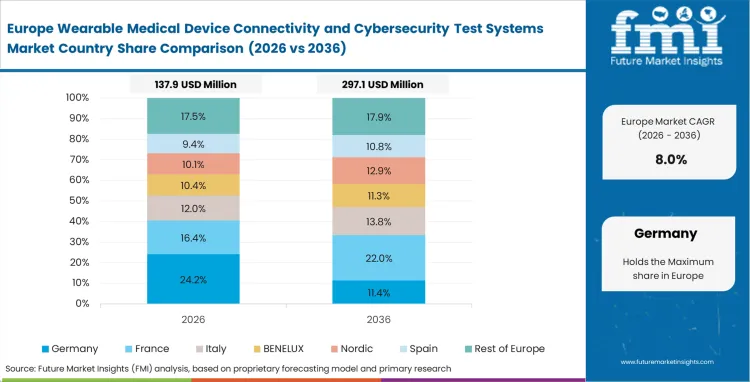
Medical Device Regulation (MDR) implementation in Europe forces a complete re-evaluation of legacy hardware that previously bypassed strict cybersecurity checks. Certification managers face intense bottlenecks at Notified Bodies, pushing them to invest heavily in pre-compliance screening equipment. Based on FMI's assessment, data localization laws under GDPR require precise validation of where and how telemedicine equipment transmits physiological metrics. Testers must verify that devices do not accidentally route encrypted patient data through non-compliant international servers during standard operation.
- Germany: The country is poised to expand at a CAGR of 11.6% through 2036, due to test lab directors building high-capacity RF chambers to service the massive local medical manufacturing base. Upgrading local testing capacity resolves the certification backlog that currently stifles regional innovation.
- United Kingdom: Procurement heads at the NHS enforce strict procurement frameworks that mandate comprehensive wireless interference testing, pushing the United Kingdom market sector expected to register a CAGR of 10.9% through 2036. This structural reality separates compliant suppliers from those unable to guarantee secure clinical connectivity.
FMI assesses, the expansive vision of Europe’s industry mirrors this push toward extreme data sovereignty and local validation. Manufacturers looking to sell across these borders must build or rent testing infrastructure that proves their hardware respects both regional medical device regulations and strict data privacy mandates.
Asia-Pacific Wearable Medical Device Connectivity and Cybersecurity Test Systems Market Analysis
Rapid growth in domestic medical manufacturing is pushing Asian suppliers to expand specialized testing infrastructure at a much faster pace. Operations managers at large contract manufacturing sites are embedding protocol validation into production lines so connectivity defects can be identified before devices move into export channels. FMI’s assessment indicates that the race to build scale in connected drug delivery devices is forcing suppliers across Asia to satisfy both local compliance rules and Western regulatory expectations. Testing capacity is expanding in parallel, supported by government funding for equipment that can raise domestic products to stricter global cybersecurity benchmarks.
- China: National standards are evolving quickly, leaving local OEMs little choice but to replace aging test rigs with systems that can handle advanced cryptographic validation. China is forecast to register a CAGR of 13.4% through 2036 in wearable device cybersecurity validation. This replacement cycle is creating strong sales potential for global vendors supplying higher-end test platforms.
- India: The country’s software engineering base continues to strengthen its position in outsourced security testing. Demand for wearable device cybersecurity validation in India is likely to increase at a CAGR of 12.9% over the forecast period, as medical device manufacturers tap local firms for penetration testing and software assurance work. Competitive strength in these hubs will depend heavily on access to advanced validation systems.
- South Korea: Close alignment between telecom providers and medical technology developers is lifting the sophistication of local testing requirements. The wearable device cybersecurity validation market in South Korea is expected to expand at a CAGR of 10.5% from 2026 to 2036, supported by work around high-speed cellular connectivity and real-time device communication performance. This environment favors suppliers that can validate demanding 5G-linked healthcare applications.
- Japan: Precision engineering capabilities continue to support the country’s role in advanced healthcare device testing. Wearable device cybersecurity validation demand in Japan is set to rise at a CAGR of 10.1% during the assessment period. Engineers are adapting sensitive measurement tools to test flexible wearable antennas, while dependable RF testing remains important for products designed around elderly care and long-term health monitoring.
FMI’s report also covers wider trends across Asia Pacific and Europe. Regulatory changes at the national level will continue to shape equipment procurement cycles across emerging medical manufacturing hubs.
Competitive Aligners for Market Players
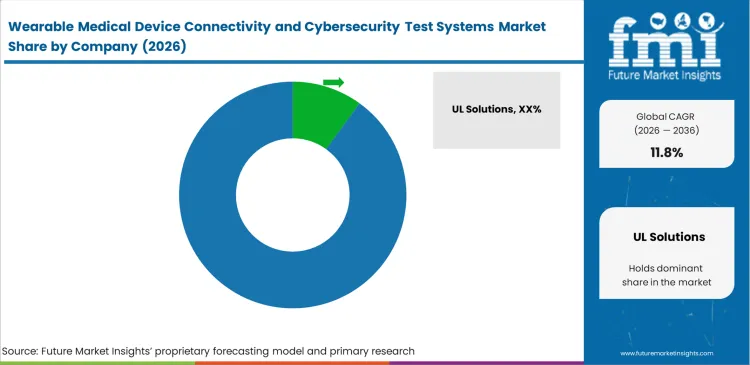
Equipment suppliers win contracts based on how quickly they update their security testing software to match new wireless rules. Engineers looking for a medical device tester prioritize systems that download fresh Bluetooth or Wi-Fi security standards the day they are published. Companies like Keysight Technologies and Rohde & Schwarz grow their customer base by ensuring their software catches newly discovered connected diagnostics flaws immediately. This speed lets medical device makers check for network threats that were identified just days ago.
Established testing companies keep their clients because regulators already trust their report formats. FMI notes that a new testing vendor has a hard time convincing a medical brand to switch systems if the old equipment already prints out compliance paperwork that the FDA approves without question. Large testing firms use this familiarity to their advantage by selling the physical radio testing machines together with the specific software that writes these trusted reports. This combined package makes it difficult for buyers to leave the ecosystem.
Device makers try to avoid getting trapped with a single supplier by mixing free security scanning tools with paid radio testing equipment. Lab managers want their physical testing machines to share data easily with outside security software. They refuse to buy into systems that limit them to one company's programs when evaluating patient monitoring devices. Equipment builders who try to lock buyers into closed software setups are losing sales to flexible testing platforms that plug easily into the security networks already running inside hospitals.
Key Players in Wearable Medical Device Connectivity and Cybersecurity Test Systems Market
- UL Solutions
- Intertek
- SGS
- TÜV SÜD
- DEKRA
- Keysight Technologies
- Rohde & Schwarz
Scope of the Report
| Metric | Value |
|---|---|
| Quantitative Units | USD 550 million to USD 1,680 million, at a CAGR of 11.8% |
| Market Definition | The wearable medical device connectivity and cybersecurity test systems market consists of validation tools that verify medical sensors transmit data reliably and resist cyber threats. Frameworks simulate clinical interference and cyberattacks to ensure patient data remains protected. |
| Segmentation | Test Focus, Connectivity Protocol, Deployment Mode, End User, Wearable Class |
| Regions Covered | North America, Latin America, Europe, East Asia, South Asia, Oceania, Middle East and Africa |
| Countries Covered | United States, Canada, Brazil, Mexico, Germany, United Kingdom, France, Spain, Italy, China, Japan, South Korea, India, Australia, New Zealand, GCC Countries, South Africa |
| Key Companies Profiled | UL Solutions, Intertek, SGS, TÜV SÜD, DEKRA, Keysight Technologies, Rohde & Schwarz |
| Forecast Period | 2026 to 2036 |
| Approach | Annual capital expenditure on validation equipment by medical device developers and third-party certification labs. |
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
Segments
Test Focus
- Connectivity validation
- Cybersecurity testing
- Interoperability testing
- Performance verification
- Compliance documentation
Connectivity Protocol
- Bluetooth LE
- Wi-Fi
- Cellular
- NFC
- UWB
Deployment Mode
- Lab systems
- Cloud platforms
- Hybrid systems
- Embedded tools
- Portable kits
End User
- OEMs
- Test labs
- Hospitals
- Design firms
- CROs
Wearable Class
- Monitoring patches
- Smartwatches
- CGM wearables
- Cardiac wearables
- Therapy wearables
Regions:
- Asia Pacific
- India
- China
- Japan
- South Korea
- Indonesia
- Australia & New Zealand
- ASEAN
- Rest of Asia Pacific
- Europe
- Netherlands
- Germany
- Italy
- France
- United Kingdom
- Spain
- Benelux
- Nordics
- Central & Eastern Europe
- Rest of Europe
- North America
- United States
- Canada
- Mexico
- Latin America
- Brazil
- Argentina
- Chile
- Rest of Latin America
- Middle East & Africa
- Kingdom of Saudi Arabia
- United Arab Emirates
- South Africa
- Turkey
- Rest of Middle East & Africa
Bibliography
- U.S. Food and Drug Administration. (2026). Cybersecurity in medical devices: Quality management system considerations and content of premarket submissions.
- National Institute of Standards and Technology. (2024). The NIST Cybersecurity Framework (CSF) 2.0 (NIST CSWP 29).
- International Medical Device Regulators Forum, Artificial Intelligence/Machine Learning-enabled Working Group. (2025). Good machine learning practice for medical device development: Guiding principles.
- Freyer, O., Jahed, F., Ostermann, M., Rosenzweig, C., Werner, P., & Gilbert, S. (2024). Consideration of cybersecurity risks in the benefit-risk analysis of medical devices: Scoping review. Journal of Medical Internet Research, 26, e65528.
- Bignami, E. G., Fornaciari, A., Fedele, S., Madeo, M., Panizzi, M., Marconi, F., Cerdelli, E., & Bellini, V. (2025). Wearable devices in healthcare beyond the one-size-fits all paradigm. Sensors, 25(20), 6472. doi:10.3390/s25206472
- Kaur, R., Shahrestani, S., & Ruan, C. (2024). Security and privacy of wearable wireless sensors in healthcare: A systematic review. Computer Networks and Communications, 2(1), 27–52. doi:10.37256/cnc.2120243852
- Trivedi, J., Isoaho, J., & Mohammad, T. (2024). A cloud-based secure architecture for remote patient monitoring integrating OPC UA and human digital twin. Procedia Computer Science. doi:10.1016/j.procs.2024.11.107
This bibliography is provided for reader reference. The full FMI report contains the complete reference list with primary source documentation.
Frequently Asked Questions
What is the valuation of the Wearable Medical Device Connectivity and Cybersecurity Test Systems industry in 2026?
Sales are expected to cross USD 550 million in 2026, signaling a massive shift toward internalizing compliance validation prior to formal regulatory submission.
What is the expected growth rate for this sector?
Demand outlook carries total valuation forward at a CAGR of 11.8% through 2036.
What will be the total valuation by 2036?
Sustained investment lifts the cumulative revenue to USD 1,680 million by 2036.
What testing is required for connected wearable medical devices?
Regulators demand rigorous RF coexistence validation combined with continuous cryptographic fuzzing to ensure both signal stability and data security.
How do you validate cybersecurity in wearable medical devices?
Engineers execute simulated attacks on network handshakes, verifying that over-the-air firmware updates remain encrypted against unauthorized interception.
Why does connectivity validation lead the test focus segment?
Engineers prioritize vital signs monitoring devices signal integrity first because a dropped connection poses an immediate physical risk compared to a delayed data breach.
What drives the adoption of Bluetooth LE testing?
Power constraints dictate that disposable patches rely on this low-energy protocol to pair with patient smartphones.
Why do lab systems dominate the deployment mode?
Regulatory bodies reject transmission data unless it is captured inside shielded physical enclosures that eliminate background radio noise.
What specific operational challenge do OEMs face without internal testing?
Software teams miss launch windows if they must wait weeks for external labs to validate weekly firmware security patches.
Why are monitoring patches difficult to validate?
Flexible antennas change their transmission characteristics when bent by patient movement or degraded by bodily fluids.
What structural difference exists between China and Germany in this sector?
China focuses heavily on rapid domestic standardization for mass manufacturing, whereas Germany prioritizes strict data routing compliance under GDPR.
How does zero-trust architecture affect device sales?
Purchasing departments reject otherwise functional PPG biosensors if the hardware fails internal hospital network authentication handshakes.
Why do test labs purchase hybrid platforms?
Combining physical radio testing with cryptographic fuzzing reduces the total time required for complete device certification.
What hidden cost emerges during Bluetooth wearable validation?
Testers must validate the security of the commercial consumer phone acting as the relay, not just the medical sensor.
How do flexible antennas impact testing economics?
Component buyers must source highly durable radio chips that survive physical stress while remaining cheap enough to discard.
Why do startups struggle with regulatory RF testing?
Relying purely on cloud-based software simulations fails to account for the physical realities of biopotential sensor antenna radiation patterns.
What drives the integration of automated fuzzing tools?
Software engineers require systems that can inject corrupted data packets seamlessly over active wireless connections to expose code flaws.
How do device updates complicate validation?
Security architects must perform full regression testing to ensure a new cryptographic patch does not break existing network pairing capabilities.
Why is third-party certification still mandatory despite internal OEM testing?
Regulatory agencies demand independent verification from recognized labs to prevent conflicts of interest in final safety audits.
What specific vulnerability do modern testing protocols target?
Engineers use advanced analyzers to detect unauthorized interception points when physiological data transfers from a patient to a cloud server.
How does physical patient movement impact connectivity testing?
Technicians use automated rotation rigs to map signal drops dynamically as the simulated patient orientation shifts.
What defines the competitive advantage of leading test equipment vendors?
Market leaders update their protocol libraries instantly when standards bodies release new medical device tester security specifications.
Why is radio frequency coexistence testing critical for hospitals?
Intensive care units feature dense radio environments that frequently overwhelm standard wireless channels and cause critical data loss.
How do data localization laws impact equipment testers?
Validation engineers must prove that medical devices never accidentally route encrypted European patient data through non-compliant international servers.
Table of Content
- Executive Summary
- Global Market Outlook
- Demand to side Trends
- Supply to side Trends
- Technology Roadmap Analysis
- Analysis and Recommendations
- Market Overview
- Market Coverage / Taxonomy
- Market Definition / Scope / Limitations
- Research Methodology
- Chapter Orientation
- Analytical Lens and Working Hypotheses
- Market Structure, Signals, and Trend Drivers
- Benchmarking and Cross-market Comparability
- Market Sizing, Forecasting, and Opportunity Mapping
- Research Design and Evidence Framework
- Desk Research Programme (Secondary Evidence)
- Company Annual and Sustainability Reports
- Peer-reviewed Journals and Academic Literature
- Corporate Websites, Product Literature, and Technical Notes
- Earnings Decks and Investor Briefings
- Statutory Filings and Regulatory Disclosures
- Technical White Papers and Standards Notes
- Trade Journals, Industry Magazines, and Analyst Briefs
- Conference Proceedings, Webinars, and Seminar Materials
- Government Statistics Portals and Public Data Releases
- Press Releases and Reputable Media Coverage
- Specialist Newsletters and Curated Briefings
- Sector Databases and Reference Repositories
- FMI Internal Proprietary Databases and Historical Market Datasets
- Subscription Datasets and Paid Sources
- Social Channels, Communities, and Digital Listening Inputs
- Additional Desk Sources
- Expert Input and Fieldwork (Primary Evidence)
- Primary Modes
- Qualitative Interviews and Expert Elicitation
- Quantitative Surveys and Structured Data Capture
- Blended Approach
- Why Primary Evidence is Used
- Field Techniques
- Interviews
- Surveys
- Focus Groups
- Observational and In-context Research
- Social and Community Interactions
- Stakeholder Universe Engaged
- C-suite Leaders
- Board Members
- Presidents and Vice Presidents
- R&D and Innovation Heads
- Technical Specialists
- Domain Subject-matter Experts
- Scientists
- Physicians and Other Healthcare Professionals
- Governance, Ethics, and Data Stewardship
- Research Ethics
- Data Integrity and Handling
- Primary Modes
- Tooling, Models, and Reference Databases
- Desk Research Programme (Secondary Evidence)
- Data Engineering and Model Build
- Data Acquisition and Ingestion
- Cleaning, Normalisation, and Verification
- Synthesis, Triangulation, and Analysis
- Quality Assurance and Audit Trail
- Market Background
- Market Dynamics
- Drivers
- Restraints
- Opportunity
- Trends
- Scenario Forecast
- Demand in Optimistic Scenario
- Demand in Likely Scenario
- Demand in Conservative Scenario
- Opportunity Map Analysis
- Product Life Cycle Analysis
- Supply Chain Analysis
- Investment Feasibility Matrix
- Value Chain Analysis
- PESTLE and Porter’s Analysis
- Regulatory Landscape
- Regional Parent Market Outlook
- Production and Consumption Statistics
- Import and Export Statistics
- Market Dynamics
- Global Market Analysis 2021 to 2025 and Forecast, 2026 to 2036
- Historical Market Size Value (USD Million) Analysis, 2021 to 2025
- Current and Future Market Size Value (USD Million) Projections, 2026 to 2036
- Y to o to Y Growth Trend Analysis
- Absolute $ Opportunity Analysis
- Global Market Pricing Analysis 2021 to 2025 and Forecast 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Test Focus
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Test Focus , 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Test Focus , 2026 to 2036
- Connectivity Validation
- Cybersecurity Testing
- Others
- Connectivity Validation
- Y to o to Y Growth Trend Analysis By Test Focus , 2021 to 2025
- Absolute $ Opportunity Analysis By Test Focus , 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Connectivity Protocol
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Connectivity Protocol, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Connectivity Protocol, 2026 to 2036
- Bluetooth LE
- Wi-Fi
- Others
- Bluetooth LE
- Y to o to Y Growth Trend Analysis By Connectivity Protocol, 2021 to 2025
- Absolute $ Opportunity Analysis By Connectivity Protocol, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Deployment Mode
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Deployment Mode, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Deployment Mode, 2026 to 2036
- Lab Systems
- Cloud Platforms
- Others
- Lab Systems
- Y to o to Y Growth Trend Analysis By Deployment Mode, 2021 to 2025
- Absolute $ Opportunity Analysis By Deployment Mode, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By End User
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By End User, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By End User, 2026 to 2036
- OEMs
- CROs
- Others
- OEMs
- Y to o to Y Growth Trend Analysis By End User, 2021 to 2025
- Absolute $ Opportunity Analysis By End User, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Wearable Class
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Wearable Class, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Wearable Class, 2026 to 2036
- Monitoring Patches
- Smartwatches
- Others
- Monitoring Patches
- Y to o to Y Growth Trend Analysis By Wearable Class, 2021 to 2025
- Absolute $ Opportunity Analysis By Wearable Class, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Region
- Introduction
- Historical Market Size Value (USD Million) Analysis By Region, 2021 to 2025
- Current Market Size Value (USD Million) Analysis and Forecast By Region, 2026 to 2036
- North America
- Latin America
- Western Europe
- Eastern Europe
- East Asia
- South Asia and Pacific
- Middle East & Africa
- Market Attractiveness Analysis By Region
- North America Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- USA
- Canada
- Mexico
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- Latin America Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Brazil
- Chile
- Rest of Latin America
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- Western Europe Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Germany
- UK
- Italy
- Spain
- France
- Nordic
- BENELUX
- Rest of Western Europe
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- Eastern Europe Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Russia
- Poland
- Hungary
- Balkan & Baltic
- Rest of Eastern Europe
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- East Asia Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- China
- Japan
- South Korea
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- South Asia and Pacific Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- India
- ASEAN
- Australia & New Zealand
- Rest of South Asia and Pacific
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- Middle East & Africa Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Kingdom of Saudi Arabia
- Other GCC Countries
- Turkiye
- South Africa
- Other African Union
- Rest of Middle East & Africa
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- By Country
- Market Attractiveness Analysis
- By Country
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Key Takeaways
- Key Countries Market Analysis
- USA
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Canada
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Mexico
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Brazil
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Chile
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Germany
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- UK
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Italy
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Spain
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- France
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- India
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- ASEAN
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Australia & New Zealand
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- China
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Japan
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- South Korea
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Russia
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Poland
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Hungary
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Kingdom of Saudi Arabia
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Turkiye
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- South Africa
- Pricing Analysis
- Market Share Analysis, 2025
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- USA
- Market Structure Analysis
- Competition Dashboard
- Competition Benchmarking
- Market Share Analysis of Top Players
- By Regional
- By Test Focus
- By Connectivity Protocol
- By Deployment Mode
- By End User
- By Wearable Class
- Competition Analysis
- Competition Deep Dive
- UL Solutions
- Overview
- Product Portfolio
- Profitability by Market Segments (Product/Age /Sales Channel/Region)
- Sales Footprint
- Strategy Overview
- Marketing Strategy
- Product Strategy
- Channel Strategy
- Intertek
- SGS
- TÜV SÜD
- DEKRA
- Keysight Technologies
- UL Solutions
- Competition Deep Dive
- Assumptions & Acronyms Used
List of Tables
- Table 1: Global Market Value (USD Million) Forecast by Region, 2021 to 2036
- Table 2: Global Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 3: Global Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 4: Global Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 5: Global Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 6: Global Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 7: North America Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 8: North America Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 9: North America Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 10: North America Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 11: North America Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 12: North America Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 13: Latin America Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 14: Latin America Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 15: Latin America Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 16: Latin America Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 17: Latin America Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 18: Latin America Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 19: Western Europe Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 20: Western Europe Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 21: Western Europe Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 22: Western Europe Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 23: Western Europe Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 24: Western Europe Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 25: Eastern Europe Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 26: Eastern Europe Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 27: Eastern Europe Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 28: Eastern Europe Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 29: Eastern Europe Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 30: Eastern Europe Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 31: East Asia Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 32: East Asia Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 33: East Asia Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 34: East Asia Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 35: East Asia Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 36: East Asia Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 37: South Asia and Pacific Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 38: South Asia and Pacific Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 39: South Asia and Pacific Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 40: South Asia and Pacific Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 41: South Asia and Pacific Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 42: South Asia and Pacific Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
- Table 43: Middle East & Africa Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 44: Middle East & Africa Market Value (USD Million) Forecast by Test Focus , 2021 to 2036
- Table 45: Middle East & Africa Market Value (USD Million) Forecast by Connectivity Protocol, 2021 to 2036
- Table 46: Middle East & Africa Market Value (USD Million) Forecast by Deployment Mode, 2021 to 2036
- Table 47: Middle East & Africa Market Value (USD Million) Forecast by End User, 2021 to 2036
- Table 48: Middle East & Africa Market Value (USD Million) Forecast by Wearable Class, 2021 to 2036
List of Figures
- Figure 1: Global Market Pricing Analysis
- Figure 2: Global Market Value (USD Million) Forecast 2021-2036
- Figure 3: Global Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 4: Global Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 5: Global Market Attractiveness Analysis by Test Focus
- Figure 6: Global Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 7: Global Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 8: Global Market Attractiveness Analysis by Connectivity Protocol
- Figure 9: Global Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 10: Global Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 11: Global Market Attractiveness Analysis by Deployment Mode
- Figure 12: Global Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 13: Global Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 14: Global Market Attractiveness Analysis by End User
- Figure 15: Global Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 16: Global Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 17: Global Market Attractiveness Analysis by Wearable Class
- Figure 18: Global Market Value (USD Million) Share and BPS Analysis by Region, 2026 and 2036
- Figure 19: Global Market Y-o-Y Growth Comparison by Region, 2026-2036
- Figure 20: Global Market Attractiveness Analysis by Region
- Figure 21: North America Market Incremental Dollar Opportunity, 2026-2036
- Figure 22: Latin America Market Incremental Dollar Opportunity, 2026-2036
- Figure 23: Western Europe Market Incremental Dollar Opportunity, 2026-2036
- Figure 24: Eastern Europe Market Incremental Dollar Opportunity, 2026-2036
- Figure 25: East Asia Market Incremental Dollar Opportunity, 2026-2036
- Figure 26: South Asia and Pacific Market Incremental Dollar Opportunity, 2026-2036
- Figure 27: Middle East & Africa Market Incremental Dollar Opportunity, 2026-2036
- Figure 28: North America Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 29: North America Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 30: North America Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 31: North America Market Attractiveness Analysis by Test Focus
- Figure 32: North America Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 33: North America Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 34: North America Market Attractiveness Analysis by Connectivity Protocol
- Figure 35: North America Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 36: North America Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 37: North America Market Attractiveness Analysis by Deployment Mode
- Figure 38: North America Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 39: North America Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 40: North America Market Attractiveness Analysis by End User
- Figure 41: North America Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 42: North America Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 43: North America Market Attractiveness Analysis by Wearable Class
- Figure 44: Latin America Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 45: Latin America Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 46: Latin America Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 47: Latin America Market Attractiveness Analysis by Test Focus
- Figure 48: Latin America Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 49: Latin America Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 50: Latin America Market Attractiveness Analysis by Connectivity Protocol
- Figure 51: Latin America Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 52: Latin America Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 53: Latin America Market Attractiveness Analysis by Deployment Mode
- Figure 54: Latin America Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 55: Latin America Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 56: Latin America Market Attractiveness Analysis by End User
- Figure 57: Latin America Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 58: Latin America Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 59: Latin America Market Attractiveness Analysis by Wearable Class
- Figure 60: Western Europe Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 61: Western Europe Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 62: Western Europe Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 63: Western Europe Market Attractiveness Analysis by Test Focus
- Figure 64: Western Europe Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 65: Western Europe Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 66: Western Europe Market Attractiveness Analysis by Connectivity Protocol
- Figure 67: Western Europe Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 68: Western Europe Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 69: Western Europe Market Attractiveness Analysis by Deployment Mode
- Figure 70: Western Europe Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 71: Western Europe Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 72: Western Europe Market Attractiveness Analysis by End User
- Figure 73: Western Europe Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 74: Western Europe Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 75: Western Europe Market Attractiveness Analysis by Wearable Class
- Figure 76: Eastern Europe Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 77: Eastern Europe Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 78: Eastern Europe Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 79: Eastern Europe Market Attractiveness Analysis by Test Focus
- Figure 80: Eastern Europe Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 81: Eastern Europe Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 82: Eastern Europe Market Attractiveness Analysis by Connectivity Protocol
- Figure 83: Eastern Europe Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 84: Eastern Europe Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 85: Eastern Europe Market Attractiveness Analysis by Deployment Mode
- Figure 86: Eastern Europe Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 87: Eastern Europe Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 88: Eastern Europe Market Attractiveness Analysis by End User
- Figure 89: Eastern Europe Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 90: Eastern Europe Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 91: Eastern Europe Market Attractiveness Analysis by Wearable Class
- Figure 92: East Asia Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 93: East Asia Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 94: East Asia Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 95: East Asia Market Attractiveness Analysis by Test Focus
- Figure 96: East Asia Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 97: East Asia Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 98: East Asia Market Attractiveness Analysis by Connectivity Protocol
- Figure 99: East Asia Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 100: East Asia Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 101: East Asia Market Attractiveness Analysis by Deployment Mode
- Figure 102: East Asia Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 103: East Asia Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 104: East Asia Market Attractiveness Analysis by End User
- Figure 105: East Asia Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 106: East Asia Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 107: East Asia Market Attractiveness Analysis by Wearable Class
- Figure 108: South Asia and Pacific Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 109: South Asia and Pacific Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 110: South Asia and Pacific Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 111: South Asia and Pacific Market Attractiveness Analysis by Test Focus
- Figure 112: South Asia and Pacific Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 113: South Asia and Pacific Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 114: South Asia and Pacific Market Attractiveness Analysis by Connectivity Protocol
- Figure 115: South Asia and Pacific Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 116: South Asia and Pacific Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 117: South Asia and Pacific Market Attractiveness Analysis by Deployment Mode
- Figure 118: South Asia and Pacific Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 119: South Asia and Pacific Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 120: South Asia and Pacific Market Attractiveness Analysis by End User
- Figure 121: South Asia and Pacific Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 122: South Asia and Pacific Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 123: South Asia and Pacific Market Attractiveness Analysis by Wearable Class
- Figure 124: Middle East & Africa Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 125: Middle East & Africa Market Value Share and BPS Analysis by Test Focus , 2026 and 2036
- Figure 126: Middle East & Africa Market Y-o-Y Growth Comparison by Test Focus , 2026-2036
- Figure 127: Middle East & Africa Market Attractiveness Analysis by Test Focus
- Figure 128: Middle East & Africa Market Value Share and BPS Analysis by Connectivity Protocol, 2026 and 2036
- Figure 129: Middle East & Africa Market Y-o-Y Growth Comparison by Connectivity Protocol, 2026-2036
- Figure 130: Middle East & Africa Market Attractiveness Analysis by Connectivity Protocol
- Figure 131: Middle East & Africa Market Value Share and BPS Analysis by Deployment Mode, 2026 and 2036
- Figure 132: Middle East & Africa Market Y-o-Y Growth Comparison by Deployment Mode, 2026-2036
- Figure 133: Middle East & Africa Market Attractiveness Analysis by Deployment Mode
- Figure 134: Middle East & Africa Market Value Share and BPS Analysis by End User, 2026 and 2036
- Figure 135: Middle East & Africa Market Y-o-Y Growth Comparison by End User, 2026-2036
- Figure 136: Middle East & Africa Market Attractiveness Analysis by End User
- Figure 137: Middle East & Africa Market Value Share and BPS Analysis by Wearable Class, 2026 and 2036
- Figure 138: Middle East & Africa Market Y-o-Y Growth Comparison by Wearable Class, 2026-2036
- Figure 139: Middle East & Africa Market Attractiveness Analysis by Wearable Class
- Figure 140: Global Market - Tier Structure Analysis
- Figure 141: Global Market - Company Share Analysis