Medical Device Cyber Risk Quantification Market
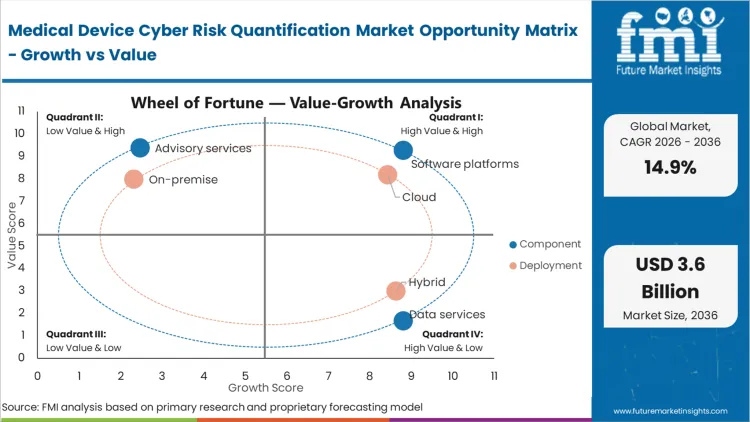
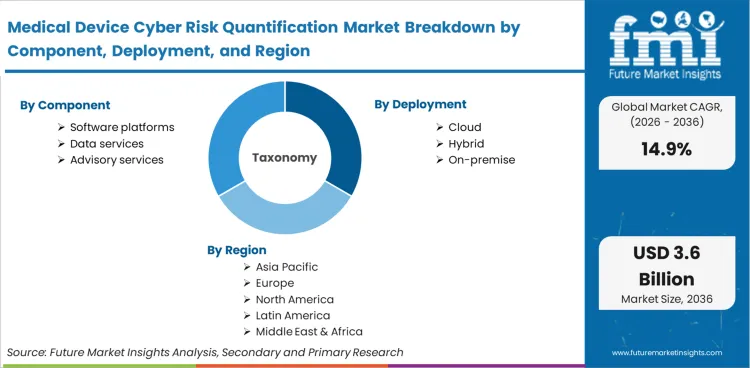
The Medical Device Cyber Risk Quantification Market Is Segmented By Component (Software Platforms, Data Services, Advisory Services), Deployment (Cloud, Hybrid, On-Premise), Buyer Type (Providers, Manufacturers, Group Purchasing), Use Case (Risk Scoring, SBOM Analysis, Vulnerability Prioritization, Compliance Evidence, Board Reporting), Asset Scope (Connected Devices, Standalone Devices, Mixed Fleets), And Region. Forecast For 2026 To 2036.
Historical Data Covered: 2016 to 2024 | Base Year: 2025 | Estimated Year: 2026 | Forecast Period: 2027 to 2036
Medical Device Cyber Risk Quantification Market Size, Market Forecast and Outlook By FMI

The medical device cyber risk quantification market surpassed the valuation of USD 0.7 billion in 2025, with industry demand poised to reach USD 0.9 billion in 2026 at a CAGR of 14.9% during forecast years. Regulatory mandates surrounding clinical infrastructure carry cumulative market growth to USD 3.6 billion through 2036 as hospital networks rely on the latest medical device cyber risk quantification forecast to transition from passive scanning to active exposure calculation.
Summary of Medical Device Cyber Risk Quantification Market
- Medical Device Cyber Risk Quantification Market Definition
- Automated IoMT risk quantification translates technical vulnerabilities across clinical hardware fleets into actionable financial and patient safety exposure metrics.
- Demand Drivers in the Market
- Ransomware attacks targeting critical care units force hospital boards to mandate quantified financial exposure reporting.
- Regulatory agencies compel diagnostic equipment manufacturers to supply dynamic vulnerability tracking capabilities.
- Medical malpractice insurers require objective cyber hygiene scores before renewing coverage for integrated delivery networks.
- Key Segments Analyzed in the FMI Report
- Software Platforms: 62.0% share in 2026, driven by continuous monitoring requirements across medical devices.
- Cloud: Anticipated to lead Deployment with a 58% share in 2026, relying on centralized threat intelligence aggregation.
- Providers: Dominates the Buyer Type with a 54% share in 2026, absorbing direct operational disruption costs.
- Risk Scoring: 29.0% share in 2026, satisfying immediate board-level reporting mandates.
- Connected Devices: 67.0% share in 2026, presenting highest lateral movement risks.
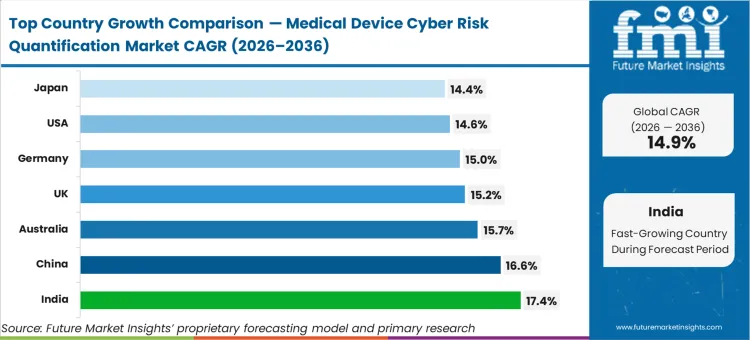
- India: A CAGR value of 17.4%, reflecting rapid digitization across private hospital chains.
- Analyst Opinion at FMI
- Sabyasachi Ghosh, Principal Analyst, Healthcare, at FMI, observes that, "Clinical engineering leaders operate under a fundamental paradox regarding asset visibility. Standard IT doctrine assumes discovering every device reduces overall organizational risk. Within hospital environments, uncovering thousands of legacy imaging machines running unsupported operating systems instantly creates unmanageable compliance liabilities without providing any actual remediation pathway. Boards demand risk quantification assuming it yields security, but initial deployment actually multiplies legal exposure by documenting known, uncatchable flaws. True value emerges only when platforms integrate clinical context, allowing clinical GenAI safety monitoring tools to prioritize vulnerabilities based on patient proximity rather than pure CVSS severity scores."
- Strategic Implications / Executive Takeaways
- Hospital CISOs must shift procurement criteria from simple asset discovery toward automated clinical workflow impact assessment.
- Diagnostic equipment manufacturers face mandatory SBOM delivery requirements delaying new product launches if undocumented.
- Cyber insurance underwriters require real-time risk telemetry to price policies accurately for large regional health networks.
- Methodology
- Baseline sizing relies upon total installed base estimates for connected clinical diagnostic equipment.
- Growth models incorporate implementation timelines for recent FDA and MDR cybersecurity mandates.
- Primary interviews with clinical engineering heads validate specific software platform replacement cycles.
- Secondary verification utilizes public hospital data breach financial impact filings.
Clinical engineering directors face an immediate compliance deadline regarding legacy equipment protection. Regulatory bodies now require continuous mathematical proof that hospital networks can isolate compromised diagnostic machines before lateral movement occurs, a shift that turns subjective security estimates into objective baseline requirements for digital healthcare operations. Facilities must accurately quantify cyber risk for medical devices or risk halting procurement approvals for high-value diagnostic imaging suites. What cybersecurity teams frequently misjudge is how heavily clinical workflow disruption weighs against pure vulnerability severity during patching protocols.
Passing regulatory threshold audits triggers self-reinforcing adoption across regional health networks. Once an integrated delivery network implements standardized scoring for its entire infusion pump fleet, neighboring facilities face immediate legal liability if they retain manual assessment protocols. This cascading standard of care transforms discretionary purchases of a medical device security platform into mandatory operational expenses for connected drug delivery devices.
India tracks at 17.4% as private hospital chains consolidate disparate IT networks, while China expands at 16.6% following state-mandated security overhauls in Tier 1 clinical centers. Australia grows at 15.7% on strict data sovereignty enforcement. United Kingdom demand advances at 15.2% due to NHS digital modernization directives. Germany records 15.0% as local data protection laws force continuous asset discovery. United States adoption hits 14.6% under intense ransomware targeting. Japan scales at 14.4% relying upon aging population care automation. Divergent growth rates reflect an underlying split between nations building new digital hospitals versus those patching legacy infrastructure.
Medical Device Cyber Risk Quantification Market Definition
Core medical device cyber risk quantification calculates exact financial and operational exposure levels tied to clinical hardware vulnerabilities. This discipline replaces qualitative threat matrices with dynamic probability algorithms mapping specific exploit vectors against patient safety impacts. Modern architecture analyzes global medical electronics telemetry to produce auditable liability scores.
Medical Device Cyber Risk Quantification Market Inclusions
Continuous asset discovery protocols fall within scope alongside software bill of materials ingestion engines. Algorithms driving a comprehensive medical device risk management platform represent primary revenue generators. Automated compliance reporting modules tailored for healthcare IT outsourcing environments constitute critical functional components evaluated here.
Medical Device Cyber Risk Quantification Market Exclusions
General enterprise IT security platforms lacking specific FDA or MDR compliance frameworks remain outside FMI analysis boundaries. Traditional network firewalls provide perimeter defense rather than asset-specific risk calculation. Endpoint detection systems deployed on standard hospital administrative computers do not qualify without dedicated clinical protocol parsing capabilities.
Medical Device Cyber Risk Quantification Market Research Methodology
- Primary Research: Chief Information Security Officers and Clinical Engineering Directors at Tier-1 health systems
- Desk Research: FDA Premarket Cybersecurity guidelines, SBOM registries, and MDR compliance databases
- Market-Sizing and Forecasting: Connected clinical asset deployment volumes across major regional hospital networks
- Data Validation and Update Cycle: Independent ransomware incident reports matching specific medical equipment vulnerabilities
Segmental Analysis
Medical Device Cyber Risk Quantification Market Analysis by Component
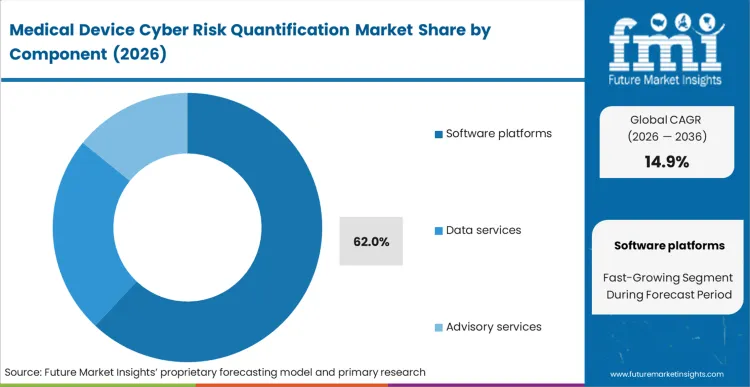
Clinical engineering teams face an impossible task attempting to manage thousands of static vulnerability reports manually when patient safety hangs in the balance. Procurement directors at large health systems prioritize continuous compliance tracking, driving Software platforms to capture a 62.0% share as these engines ingest real-time network traffic directly from portable medical devices. Translating raw packet data into prioritized remediation workflows proves far more effective than relying on standalone advisory consulting. The factor that this software dominance obscures is how heavily these automated platforms still rely upon human clinical engineers to determine if applying a software patch will inadvertently alter a physiological monitor's calibration. Purchasing disconnected point solutions results in critical alert fatigue, ultimately increasing patient risk through missed notifications.
- Telemetry Aggregation: Software ingests continuous network traffic. Clinical engineering directors avoid manual audit requirements.
- Workflow Integration: Platforms connect directly with existing hospital IT ticketing systems. IT managers reduce mean time to remediation.
- Calibration Preservation: Engines flag vulnerabilities without forcing immediate patches. Radiology administrators maintain uninterrupted diagnostic scheduling.
Medical Device Cyber Risk Quantification Market Analysis by Deployment
Centralized threat intelligence sharing, holding a 58.0% of the deployment category, explains why Cloud architectures capture dominant market share. FMI observes that isolated hospital networks cannot independently detect zero-day exploits targeting specific infusion pump firmware versions fast enough. Cloud engines pool risk management data across hundreds of healthcare facilities globally, applying predictive analytics to identify lateral movement patterns before localized breaches occur. Chief Information Security Officers leverage this collective defense mechanism to populate a centralized hospital medical device cyber risk dashboard protecting decentralized outpatient clinics lacking dedicated IT personnel. On-premise installations remain necessary only for highly restricted military or state-operated hospitals where strict data sovereignty laws absolutely forbid external telemetry transmission. Delayed cloud migration forces localized IT teams into reactive firefighting postures during coordinated ransomware campaigns.
- Threat Pooling: Cloud instances share anonymized attack signatures globally. Network security officers prevent zero-day lateral movement.
- Remote Provisioning: Updates push instantly to decentralized outpatient facilities. Clinic administrators maintain compliance without local IT staff.
- Sovereignty Friction: State regulations block external data transmission. Government hospital directors face higher local infrastructure costs.
Medical Device Cyber Risk Quantification Market Analysis by Buyer Type
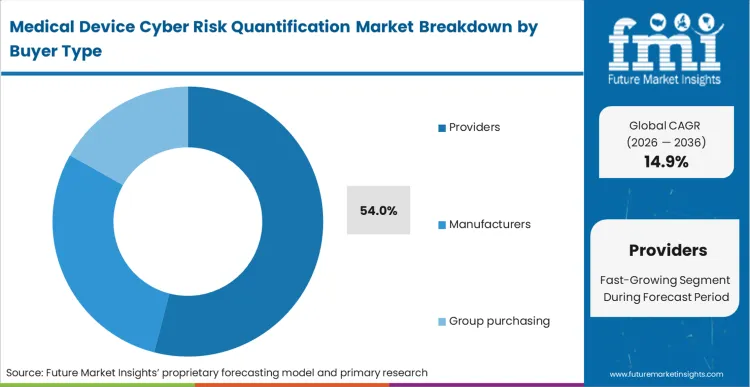
Direct financial liability for patient harm drives hospitals to absorb massive regulatory fines and reputational damage when unsecured medical device technologies compromise protected health information. Hospital procurement heads deploy healthcare provider medical device cyber risk tools to justify increased security budget requests before skeptical finance committees. FMI's analysis indicates this provider-heavy metric underestimates how rapidly medical equipment manufacturers are internalizing these tools during product development phases to avoid costly post-market recalls, leading providers to account for 54.0% share, thereby, relying purely on manufacturer-provided security assurances leaving hospital networks legally exposed when zero-day vulnerabilities emerge unexpectedly.
- Budget Justification: Quantification tools translate cyber risks into financial exposure metrics. Hospital finance directors approve necessary security expenditures.
- Liability Transfer: Clear risk documentation proves hospital due diligence. Legal compliance officers successfully defend against negligence claims following breaches.
- Pre-Market Testing: Manufacturers embed scoring algorithms during R&D. Product development heads prevent delayed FDA approvals.
Medical Device Cyber Risk Quantification Market Analysis By Use Case
Hospital board members require digestible metrics summarizing total organizational exposure rather than highly technical vulnerability lists. Fiduciary responsibility mandates propel Risk scoring to 29.0% share. Advanced medical device cyber risk score methodology synthesizes complex IT metrics with clinical asset criticality, presenting healthcare interoperability solutions vulnerabilities in pure financial terms. FMI analysts note that relying solely on aggregate scores creates false security if underlying SBOM data remains outdated or incomplete. Clinical IT directors failing to implement granular SBOM medical device risk scoring face complete operational paralysis when federal agencies announce widespread vulnerabilities in common third-party software libraries.
- Board Communication: Algorithms convert technical flaws into financial risk metrics. Chief Executive Officers understand true organizational exposure.
- Library Tracking: SBOM ingestion identifies hidden third-party code vulnerabilities. Software engineering leads accelerate targeted patching cycles.
- Regulatory Proof: Automated evidence generation satisfies continuous audit requirements. Compliance officers avoid punitive regulatory fines.
Medical Device Cyber Risk Quantification Market Analysis By Asset Scope
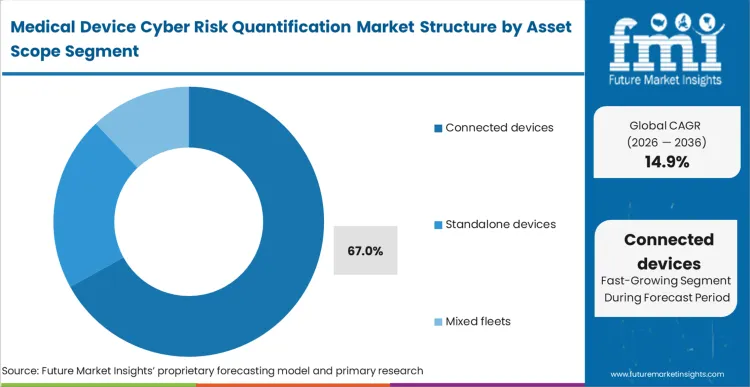
With a commanding 67.0% share, connected devices force network architects to prioritize securing active communication channels against malicious ingress. Wireless infusion pumps and mobile telemetry units constantly exchange data across hospital networks, creating thousands of potential bridgeheads into highly restricted patient database servers. Based on FMI's assessment, isolating focus entirely on wireless compliance monitoring devices leaves critical standalone diagnostic machines vulnerable to physical USB-based malware insertion. Overlooking mixed fleet dynamics forces biomedical engineers to establish separate postmarket medical device cyber risk monitoring protocols. Splitting these defensive strategies drastically increases administrative overhead and guarantees human error during localized malware outbreaks.
- Ingress Monitoring: Wireless devices undergo continuous packet inspection. Network architects identify anomalous data exfiltration attempts immediately.
- Physical Isolation: Standalone machines require specialized USB gateway scanning. Biomedical engineers prevent localized malware outbreaks.
- Protocol Unification: Mixed fleet platforms consolidate diverse asset tracking. Clinical engineering directors streamline total inventory management.
Medical Device Cyber Risk Quantification Market Drivers, Restraints, and Opportunities
Ransomware syndicates deliberately targeting critical care environments force hospital administrators to quantify their exact financial exposure. Threat actors realize disrupting clinical operations guarantees faster ransom payments than simply stealing encrypted data files. Chief Information Security Officers utilize quantification platforms because completing an FDA 524B medical device cybersecurity risk assessment mathematically proves that upgrading legacy MRI operating systems costs significantly less than absorbing projected downtime losses during an attack. Purchasing these tools accelerates as AI enabled medical devices introduce complex neural network vulnerabilities into clinical settings, demanding dynamic medical device vulnerability prioritization algorithms that traditional IT security scanners simply cannot provide.
Fragmented proprietary communication protocols across different medical equipment manufacturers severely restrict comprehensive network visibility. Clinical engineering directors struggle to aggregate risk data because aging diagnostic machines utilize closed, undocumented operating systems that block standard security scanning tools. FMI's analysis shows this fundamental interoperability friction prevents health systems from achieving unified risk dashboards, leaving invisible gaps in their exposure calculations. While artificial intelligence in healthcare promises eventual protocol normalization, current hospital IT teams must deploy expensive customized gateway appliances to translate proprietary telemetry into standardized risk metrics.
Opportunities in Medical Device Cyber Risk Quantification Market
- Insurance Integration: Real-time risk telemetry allows dynamic cyber insurance premium pricing. Hospital finance directors lower overhead costs by demonstrating verifiable cyber resilience and a strong ROI of medical device security platform investments.
- Procurement Gating: Risk algorithms evaluate new equipment prior to purchase finalization. Supply chain executives block inherently vulnerable diagnostic machines from entering hospital environments.
- Clinical Workflow Mapping: Integrating threat data with healthcare business intelligence predicts specific patient care disruptions. Chief Medical Officers reroute critical procedures before cyber incidents impact patient outcomes.
Regional Analysis
Based on regional analysis, Medical Device Cyber Risk Quantification is segmented into North America, Europe, Asia-Pacific & ASEAN across 40 plus countries. Global variance in clinical digitization and regulatory maturity dictates the adoption curves for cyber risk quantification tools across diverse geographic theaters. While some nations actively patch legacy infrastructure against immediate ransomware threats, others proactively build mathematical security frameworks directly into newly constructed digital hospital networks.
.webp)
| Country | CAGR (2026 to 2036) |
|---|---|
| India | 17.4% |
| China | 16.6% |
| Australia | 15.7% |
| United Kingdom | 15.2% |
| Germany | 15.0% |
| United States | 14.6% |
| Japan | 14.4% |
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
North America Medical Device Cyber Risk Quantification Market Analysis
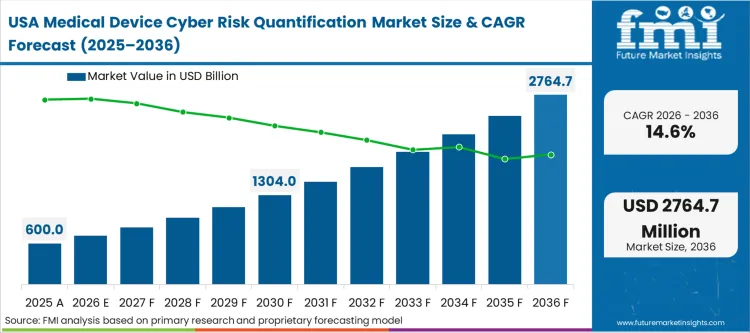
High-profile ransomware attacks targeting large regional providers currently accelerate adoption across the continent, as hospital boards aggressively demand mathematical proof of resilience. Local cybersecurity insurance underwriters now refuse coverage renewals without granular, device-level risk scoring, turning precise vulnerability quantification into a fundamental requirement for continued financial survival. Regulatory bodies concurrently tie Medicare reimbursement rates to verifiable IT security postures, which forces clinical engineering directors to deploy quantification software across all connected infrastructure. United States hospitals operate under this intense scrutiny from federal agencies that mandate strict, uncompromising cybersecurity performance goals. Failing to map specific hardware flaws to patient proximity ultimately exposes these clinical networks to massive liabilities that generic IT scanners cannot mitigate.
- United States: Experiencing a 14.6% CAGR, the domestic market expands rapidly as strict federal reimbursement ties force immediate compliance. Hospital financial officers prioritize these quantification platforms specifically to avoid massive Medicare penalty deductions tied to poor cyber hygiene. Network architects within integrated delivery systems cannot afford to manually audit thousands of legacy imaging machines running unsupported operating systems. By translating technical vulnerabilities into actionable financial exposure metrics, clinical IT leads successfully secure the necessary budget approvals from skeptical finance committees. Automating these workflow, in the end, impact assessments prevents the complete operational paralysis that follows widespread clinical data breaches.
FMI's report includes Canadian facilities navigating similar provincial health data compliance standards. Cross-border healthcare partnerships necessitate unified vulnerability scoring methodologies across regional lines.
Europe Medical Device Cyber Risk Quantification Market Analysis
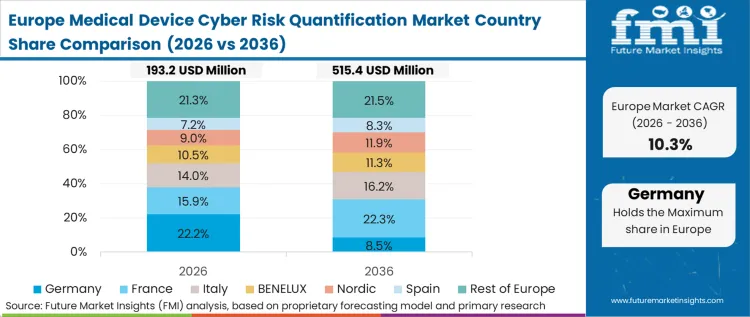
Centralized healthcare administration models define the continent's deployment strategies, allowing rapid, nationwide rollouts of vulnerability scanning tools across standardized equipment fleets. FMI analysts note that this compliance-heavy environment forces connected (RHM) remote healthcare monitoring equipment suppliers to embed risk quantification directly into their product architectures before market entry. National legislation aggressively penalizes hospital networks failing to maintain updated hardware inventories, decisively pushing IT directors toward automated scanning platforms. German healthcare facilities specifically face stringent local data protection enforcement requiring continuous asset discovery and vulnerability tracking. Meanwhile, United Kingdom modernization directives strictly compel NHS trusts to overhaul legacy clinical infrastructure with standardized, measurable security protocols.
- Germany: Clinical IT leads urgently deploy automated scanning platforms to prevent punitive national regulatory fines tied to poor asset visibility. Aggressive national data protection laws heavily mandate continuous discovery of connected medical devices across all care facilities. Driven by these strict liability pressures, the sector registers a 15.0% in CAGR value expansion as administrators move away from manual audit logs. Procurement directors focus heavily on platforms that can decipher proprietary telemetry from localized manufacturers without crashing delicate diagnostic equipment. Satisfying these continuous audit requirements allows compliance officers to maintain uninterrupted patient services while navigating the rigid local regulatory landscape.
- United Kingdom: National procurement officers actively secure volume-based platform licensing discounts by leveraging the centralized purchasing power of the health system. Modernization mandates compel NHS trusts to replace fragmented, localized security measures with unified vulnerability scoring methodologies. Hospital administrators require precise telemetry aggregation to protect newly integrated outpatient clinics that often lack dedicated local IT personnel. Chief Information Security Officers refuse proprietary black-box scoring algorithms, demanding transparent methodologies that internal data science teams can audit independently. The regional trajectory sustains a steady progression of 15.2% CAGR, because of these systemic digital infrastructure upgrades.
FMI's report includes qualitative assessments for emerging healthcare biometrics security environments across secondary European territories. These transitional environments display unique structural delays tied to limited clinical IT budgets.
Asia-Pacific & ASEAN Medical Device Cyber Risk Quantification Market Analysis
Corporate healthcare providers rapidly deploy risk scoring to standardize security postures across newly acquired regional clinics as they modernize disparate IT networks. Hospital administrators across mature technological hubs rely heavily upon robotic assistants and remote telemetry, creating vast attack surfaces requiring continuous monitoring. Government directives throughout the region frequently require localized threat intelligence hosting, which inherently restricts foreign cloud platform deployment. Australia enforces stringent data sovereignty laws dictating exactly how medical telemetry must be protected, while China implements strict state-mandated security overhauls across its rapidly expanding Tier 1 clinical centers. Japan concurrently integrates advanced quantification tools specifically to protect the highly automated care facilities that support its vulnerable aging population.
- Japan: Generating a 14.4% of CAGR trajectory, this market relies on care automation dependencies rather than purely regulatory mandates. Facility directors must maintain uninterrupted robotic patient assistance services, meaning any cyber disruption directly threatens immediate physical care delivery. Clinical engineering teams prioritize software platforms that ingest real-time network traffic from these advanced robotics without triggering false alarms. Network security officers prevent zero-day lateral movement across these hyper-connected facilities by pooling anonymized attack signatures. By calculating the exact operational exposure levels tied to hardware vulnerabilities, administrators ensure critical care pathways remain secure.
- China: Domestic security vendors capture exclusive government hospital contracts by aligning with strict state-mandated infrastructure overhauls. Clinical engineering directors must implement specialized gateway appliances capable of translating proprietary telemetry into standardized risk metrics under strict localized hosting rules. Operating within this highly regulated perimeter, the sector produces a 16.6% of CAGR driven entirely by internal modernization directives. Network architects isolate critical standalone diagnostic machines to prevent physical USB-based malware insertion across Tier 1 clinical centers. The supply chain executives, in the end, block inherently vulnerable diagnostic machines from entering these hospital environments during initial purchasing evaluations.
- India: Corporate IT directors strive to achieve unified visibility across rapidly merging clinical networks that utilize entirely different hardware brands. Private hospital consolidation forces administrators to synthesize complex IT metrics with clinical asset criticality to satisfy immediate fiduciary reporting mandates. Biomedical engineers struggle to maintain divergent security protocols unless they adopt platforms capable of managing mixed fleets effectively. Integrating threat data with broader hospital business intelligence predicts specific patient care disruptions before they occur across these vast new networks. The market yields an impressive 17.4% advancement of CAGR value, by navigating this massive wave of private clinical digitization.
- Australia: Driving a robust 15.7% CAGR momentum, strict data sovereignty enforcement dictates the fundamental architecture of deployed quantification platforms. Network architects must ensure absolute compliance with national privacy mandates by keeping all vulnerability telemetry strictly within geographic borders. Hospital procurement heads favor solutions that combine technical analytics with automated vendor risk assessment questionnaires tailored to these local laws. Software engineering leads accelerate targeted patching cycles by identifying hidden third-party code vulnerabilities deep inside proprietary vendor applications. This approach allows clinical IT directors to intercept vulnerabilities before new devices even arrive at the facility dock.
FMI's report includes broader Southeast Asian hospital networks upgrading fundamental IT architecture. Rapid urbanization forces healthcare providers to scale device tracking capabilities ahead of basic physical security implementations.
Competitive Aligners for Market Players
Incumbent security providers secure large enterprise hospital contracts by leveraging their extensive proprietary databases mapping thousands of unique medical device communication protocols. Clinical engineering directors select Claroty and Asimily because these platforms recognize specific proprietary telemetry from obscure infusion pumps and aging MRI machines without triggering disruptive network false alarms. FMI analysts note that new market entrants lack these deep signature libraries, forcing them to rely on generic IT scanning methods that often crash delicate clinical equipment during active vulnerability probes. This protocol translation capability forms a massive defensive moat shielding early medical device cyber risk quantification vendors from generic cybersecurity companies attempting cross-industry expansion.
Challengers like Censinet and Cynerio compete by deeply integrating medical device cybersecurity risk assessment software directly into broader hospital supply chain and procurement workflows. Rather than merely scanning existing networks, these platforms intercept vulnerabilities before new devices even arrive by evaluating vendor SBOMs during initial purchasing evaluations. Hospital procurement heads looking for the best medical device risk scoring platform favor solutions combining technical healthcare analytics with automated vendor risk assessment questionnaires, creating a unified barrier against unsecure hardware. Established incumbents must continuously acquire smaller workflow automation startups to prevent these agile challengers from monopolizing crucial pre-procurement security evaluation phases.
Large integrated delivery networks combat vendor lock-in by demanding open API architectures that feed specialized device intelligence into their centralized enterprise security dashboards. Chief Information Security Officers refuse proprietary black-box scoring algorithms, requiring fully transparent methodologies that internal data science teams can audit and adjust based on local clinical priorities. Structural integration mandates dictate that medical device cyber risk quantification key players must seamlessly share telemetry with broader global digital health monitoring infrastructure, shifting baseline competition away from pure asset discovery toward complete interoperability with existing enterprise incident response workflows.
Key Players in Medical Device Cyber Risk Quantification Market
- Claroty
- Asimily
- Censinet
- Cynerio
- Armis
- Forescout
- Ordr
Scope of the Report
| Metric | Value |
|---|---|
| Quantitative Units | USD 0.9 billion to USD 3.6 billion, at a CAGR of 14.9% |
| Market Definition | Core medical device cyber risk quantification calculates exact financial and operational exposure levels tied to clinical hardware vulnerabilities. This discipline replaces qualitative threat matrices with dynamic probability algorithms mapping specific exploit vectors against patient safety impacts. |
| Segmentation | Component, Deployment, Buyer Type, Use case, Asset Scope, Region |
| Regions Covered | North America, Latin America, Europe, East Asia, South Asia & Pacific, Middle East & Africa |
| Countries Covered | United States, Canada, Germany, United Kingdom, France, Italy, Spain, China, Japan, South Korea, India, ASEAN, Australia, Brazil, Mexico, GCC, South Africa |
| Key Companies Profiled | Claroty, Asimily, Censinet, Cynerio, Armis, Forescout, Ordr |
| Forecast Period | 2026 to 2036 |
| Approach | Connected clinical asset deployment volumes across major regional hospital networks |
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
Segments
Component:
- Software platforms
- Data services
- Advisory services
Deployment:
- Cloud
- Hybrid
- On-premise
Buyer Type:
- Providers
- Manufacturers
- Group purchasing
Use Case:
- Risk scoring
- SBOM analysis
- Vulnerability prioritization
- Compliance evidence
- Board reporting
Asset Scope
- Connected devices
- Standalone devices
- Mixed fleets
Regions:
- Asia Pacific
- India
- China
- Japan
- South Korea
- Indonesia
- Australia & New Zealand
- ASEAN
- Rest of Asia Pacific
- Europe
- Germany
- Italy
- France
- United Kingdom
- Spain
- Benelux
- Nordics
- Central & Eastern Europe
- Rest of Europe
- North America
- United States
- Canada
- Mexico
- Latin America
- Brazil
- Argentina
- Chile
- Rest of Latin America
- Middle East & Africa
- Kingdom of Saudi Arabia
- United Arab Emirates
- South Africa
- Turkey
- Rest of Middle East & Africa
Bibliography
- USA Food and Drug Administration. (2026, February 3). Cybersecurity in medical devices: Quality management system considerations and content of premarket submissions.
- Cybersecurity and Infrastructure Security Agency. (2024, February). Cyber threats to medical technology and communication technology protocols.
- Freyer, O., et al. (2024). Consideration of cybersecurity risks in the benefit-risk analysis of medical devices: Scoping review. Journal of Medical Internet Research.
- Bracciale, L., Riozzi, S., Panico, G., & Raso, E. (2025). Quantifying medical device cybersecurity risk with CVSS BTE. Scientific Reports.
- Svandova, K., et al. (2024). Internet of Medical Things security frameworks for risk management: A scoping review. Journal of Multidisciplinary Healthcare.
- Pritika, P., et al. (2024). Risk evaluation and attack detection in heterogeneous Internet of Medical Things using a novel risk assessment framework. Sensors.
- American Hospital Association. (2025, January 31). CISA, FDA warn of vulnerabilities in Contec patient monitors.
This bibliography is provided for reader reference. The full FMI report contains the complete reference list with primary source documentation.
This Report Addresses
- Clinical engineering compliance requirements tied to legacy medical hardware.
- Software platform penetration rates replacing manual vulnerability audit logs.
- Cloud deployment models enabling centralized zero-day threat intelligence pooling.
- Hospital procurement pressures driving quantified financial exposure metrics.
- Mixed fleet security unification bridging wireless sensors and standalone machines.
- Ransomware impacts forcing board-level visibility into diagnostic equipment risks.
- Interoperability constraints blocking unified risk dashboard creation across disparate vendors.
- Proprietary protocol translation acting as competitive moats for incumbent security vendors.
Frequently Asked Questions
What structural condition drives Software platforms to 62.0% share?
Software engines secure their dominant share by ingesting real-time network traffic directly from connected medical devices to translate raw packet data into prioritized remediation workflows, preventing clinical engineering teams from having to manage thousands of static vulnerability reports manually.
Why do Providers dominate Buyer Type with 54.0% share?
Direct financial liability for patient harm forces hospitals to deploy quantification tools that justify increased cybersecurity budgets, as networks absorb massive regulatory fines and reputational damage when unsecured diagnostic technologies compromise protected health information.
How do hospitals score medical device cyber risk?
Clinical engineering directors deploy specialized gateway appliances equipped with algorithms that translate fragmented proprietary telemetry into standardized risk metrics, effectively calculating exposure despite aging, undocumented diagnostic machine operating systems.
Why does India grow faster than other evaluated countries at 17.4%?
Rapid consolidation of private hospital chains drives growth as corporate healthcare providers deploy risk scoring to quickly standardize security postures across newly acquired regional clinics with disparate IT networks.
How to choose a medical device risk management platform?
Buyers must prioritize solutions that integrate directly with hospital supply chain and procurement workflows, allowing executives to evaluate vendor SBOMs and block inherently vulnerable diagnostic machines before they enter clinical environments.
What non-obvious reality complicates Connected devices' 67.0% share position?
Isolating focus entirely on wireless equipment leaves critical standalone diagnostic machines vulnerable to physical USB-based malware insertion, forcing biomedical engineers to maintain divergent, error-prone security protocols for mixed fleets.
Why is SBOM important in medical device cybersecurity?
SBOM ingestion drastically accelerates targeted patching cycles by identifying hidden third-party code vulnerabilities deep inside proprietary vendor applications, allowing software engineering leads to locate compromised libraries immediately without waiting for official manufacturer bulletins.
How do challengers compete against established protocol library moats?
Agile vendors compete by integrating risk quantification directly into hospital supply chain workflows, intercepting vulnerabilities through vendor SBOM evaluation during initial purchasing to block unsecure hardware before it ever enters clinical environments.
What regulations require medical device cyber risk assessment?
Regulatory bodies, aligning with FDA 524B requirements, mandate continuous mathematical proof that hospital networks can isolate compromised diagnostic machines before lateral movement occurs, meaning failure to generate these quantified exposure metrics directly halts procurement approvals.
How does calibration risk change typical vulnerability patching behavior?
Because applying software patches can inadvertently alter physiological monitor accuracy, software platforms are designed to flag vulnerabilities without forcing immediate disruptive patches, allowing radiology administrators to safely maintain diagnostic schedules.
What forces United Kingdom deployment strategies at 15.2% CAGR?
Centralized NHS modernization directives compel trusts to overhaul legacy clinical infrastructure using standardized security protocols, enabling the rapid, simultaneous deployment of vulnerability scanning tools across national equipment fleets.
Why do large delivery networks demand open API architectures from vendors?
Chief Information Security Officers demand open architectures to feed specialized device intelligence directly into centralized enterprise security dashboards, refusing proprietary black-box scoring algorithms that restrict independent internal data science audits.
How do medical equipment manufacturers utilize risk scoring platforms internally?
Product development heads embed scoring algorithms during initial R&D phases to provide verifiable security documentation that prevents delayed FDA approvals and avoids costly post-market recall cycles entirely.
What specific metric anchors baseline forecasting for this market?
Baseline forecasting is anchored by total installed base estimates for connected clinical diagnostic equipment deployed across major regional networks, dynamically adjusted for hardware replacement cycles spanning five to eight years.
Why does Germany mandate continuous asset discovery locally?
Aggressive national data protection laws heavily penalize hospital networks for failing to maintain updated hardware inventories, driving clinical IT leads to deploy automated scanning platforms specifically to prevent punitive regulatory fines tied to poor asset visibility.
How does clinical workflow integration differ from traditional IT security?
Unlike traditional IT scanners that lack medical protocol translation capabilities and frequently crash delicate equipment during active probes, healthcare-specific platforms recognize proprietary telemetry without triggering disruptive network false alarms.
What drives United States adoption at 14.6% CAGR?
Federal agencies increasingly tie Medicare reimbursement rates directly to verifiable IT security postures, compelling hospital financial officers to deploy quantification software to avoid massive penalty deductions and satisfy stringent cyber insurance renewal requirements.
How does robotic care automation impact Japanese adoption trends?
The heavy reliance on robotic assistants and remote telemetry to support aging populations creates vast attack surfaces in Japanese hospitals, requiring continuous cyber monitoring to maintain uninterrupted patient care services.
What consequence awaits hospitals failing to map vulnerabilities to patient proximity?
Uncovering thousands of legacy imaging flaws without clinical context creates unmanageable compliance liabilities, multiplying a hospital's legal exposure by documenting known, unpatchable flaws unless platforms prioritize remediation based directly on actual patient safety impacts.
How do SBOM ingestion engines accelerate targeted patching cycles?
SBOM ingestion engines accelerate patching by identifying hidden third-party code vulnerabilities deep inside proprietary vendor applications, allowing software engineering leads to locate specific compromised libraries immediately without waiting for official manufacturer security bulletins.
Why do military hospitals maintain isolated on-premise quantification installations?
Government hospital directors absorb higher local infrastructure costs to maintain isolated on-premise quantification installations because strict state data sovereignty regulations absolutely forbid external telemetry transmission to ensure highly restricted patient data never crosses international borders.
What changes structurally for cyber insurance providers utilizing this technology?
Real-time risk telemetry allows underwriters to accurately price policies based on verifiable cyber resilience rather than static annual questionnaires, fundamentally shifting the market toward dynamic premium pricing for networks demonstrating continuous threat mitigation capabilities.
Table of Content
- Executive Summary
- Global Market Outlook
- Demand to side Trends
- Supply to side Trends
- Technology Roadmap Analysis
- Analysis and Recommendations
- Market Overview
- Market Coverage / Taxonomy
- Market Definition / Scope / Limitations
- Research Methodology
- Chapter Orientation
- Analytical Lens and Working Hypotheses
- Market Structure, Signals, and Trend Drivers
- Benchmarking and Cross-market Comparability
- Market Sizing, Forecasting, and Opportunity Mapping
- Research Design and Evidence Framework
- Desk Research Programme (Secondary Evidence)
- Company Annual and Sustainability Reports
- Peer-reviewed Journals and Academic Literature
- Corporate Websites, Product Literature, and Technical Notes
- Earnings Decks and Investor Briefings
- Statutory Filings and Regulatory Disclosures
- Technical White Papers and Standards Notes
- Trade Journals, Industry Magazines, and Analyst Briefs
- Conference Proceedings, Webinars, and Seminar Materials
- Government Statistics Portals and Public Data Releases
- Press Releases and Reputable Media Coverage
- Specialist Newsletters and Curated Briefings
- Sector Databases and Reference Repositories
- FMI Internal Proprietary Databases and Historical Market Datasets
- Subscription Datasets and Paid Sources
- Social Channels, Communities, and Digital Listening Inputs
- Additional Desk Sources
- Expert Input and Fieldwork (Primary Evidence)
- Primary Modes
- Qualitative Interviews and Expert Elicitation
- Quantitative Surveys and Structured Data Capture
- Blended Approach
- Why Primary Evidence is Used
- Field Techniques
- Interviews
- Surveys
- Focus Groups
- Observational and In-context Research
- Social and Community Interactions
- Stakeholder Universe Engaged
- C-suite Leaders
- Board Members
- Presidents and Vice Presidents
- R&D and Innovation Heads
- Technical Specialists
- Domain Subject-matter Experts
- Scientists
- Physicians and Other Healthcare Professionals
- Governance, Ethics, and Data Stewardship
- Research Ethics
- Data Integrity and Handling
- Primary Modes
- Tooling, Models, and Reference Databases
- Desk Research Programme (Secondary Evidence)
- Data Engineering and Model Build
- Data Acquisition and Ingestion
- Cleaning, Normalisation, and Verification
- Synthesis, Triangulation, and Analysis
- Quality Assurance and Audit Trail
- Market Background
- Market Dynamics
- Drivers
- Restraints
- Opportunity
- Trends
- Scenario Forecast
- Demand in Optimistic Scenario
- Demand in Likely Scenario
- Demand in Conservative Scenario
- Opportunity Map Analysis
- Product Life Cycle Analysis
- Supply Chain Analysis
- Investment Feasibility Matrix
- Value Chain Analysis
- PESTLE and Porter’s Analysis
- Regulatory Landscape
- Regional Parent Market Outlook
- Production and Consumption Statistics
- Import and Export Statistics
- Market Dynamics
- Global Market Analysis 2021 to 2025 and Forecast, 2026 to 2036
- Historical Market Size Value (USD Million) Analysis, 2021 to 2025
- Current and Future Market Size Value (USD Million) Projections, 2026 to 2036
- Y to o to Y Growth Trend Analysis
- Absolute $ Opportunity Analysis
- Global Market Pricing Analysis 2021 to 2025 and Forecast 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Component
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Component , 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Component , 2026 to 2036
- Software platforms
- Data services
- Advisory services
- Software platforms
- Y to o to Y Growth Trend Analysis By Component , 2021 to 2025
- Absolute $ Opportunity Analysis By Component , 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Deployment
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Deployment, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Deployment, 2026 to 2036
- Cloud
- Hybrid
- On-premise
- Cloud
- Y to o to Y Growth Trend Analysis By Deployment, 2021 to 2025
- Absolute $ Opportunity Analysis By Deployment, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Buyer Type
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Buyer Type, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Buyer Type, 2026 to 2036
- Providers
- Manufacturers
- Group purchasing
- Providers
- Y to o to Y Growth Trend Analysis By Buyer Type, 2021 to 2025
- Absolute $ Opportunity Analysis By Buyer Type, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Use Case
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Use Case, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Use Case, 2026 to 2036
- Risk scoring
- SBOM analysis
- Vulnerability prioritization
- Compliance evidence
- Board reporting
- Risk scoring
- Y to o to Y Growth Trend Analysis By Use Case, 2021 to 2025
- Absolute $ Opportunity Analysis By Use Case, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Asset Scope
- Introduction / Key Findings
- Historical Market Size Value (USD Million) Analysis By Asset Scope, 2021 to 2025
- Current and Future Market Size Value (USD Million) Analysis and Forecast By Asset Scope, 2026 to 2036
- Connected devices
- Standalone devices
- Mixed fleets
- Connected devices
- Y to o to Y Growth Trend Analysis By Asset Scope, 2021 to 2025
- Absolute $ Opportunity Analysis By Asset Scope, 2026 to 2036
- Global Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Region
- Introduction
- Historical Market Size Value (USD Million) Analysis By Region, 2021 to 2025
- Current Market Size Value (USD Million) Analysis and Forecast By Region, 2026 to 2036
- North America
- Latin America
- Western Europe
- Eastern Europe
- East Asia
- South Asia and Pacific
- Middle East & Africa
- Market Attractiveness Analysis By Region
- North America Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- USA
- Canada
- Mexico
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- Latin America Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Brazil
- Chile
- Rest of Latin America
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- Western Europe Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Germany
- UK
- Italy
- Spain
- France
- Nordic
- BENELUX
- Rest of Western Europe
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- Eastern Europe Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Russia
- Poland
- Hungary
- Balkan & Baltic
- Rest of Eastern Europe
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- East Asia Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- China
- Japan
- South Korea
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- South Asia and Pacific Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- India
- ASEAN
- Australia & New Zealand
- Rest of South Asia and Pacific
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- Middle East & Africa Market Analysis 2021 to 2025 and Forecast 2026 to 2036, By Country
- Historical Market Size Value (USD Million) Trend Analysis By Market Taxonomy, 2021 to 2025
- Market Size Value (USD Million) Forecast By Market Taxonomy, 2026 to 2036
- By Country
- Kingdom of Saudi Arabia
- Other GCC Countries
- Turkiye
- South Africa
- Other African Union
- Rest of Middle East & Africa
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- By Country
- Market Attractiveness Analysis
- By Country
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Key Takeaways
- Key Countries Market Analysis
- USA
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Canada
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Mexico
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Brazil
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Chile
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Germany
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- UK
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Italy
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Spain
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- France
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- India
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- ASEAN
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Australia & New Zealand
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- China
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Japan
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- South Korea
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Russia
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Poland
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Hungary
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Kingdom of Saudi Arabia
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Turkiye
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- South Africa
- Pricing Analysis
- Market Share Analysis, 2025
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- USA
- Market Structure Analysis
- Competition Dashboard
- Competition Benchmarking
- Market Share Analysis of Top Players
- By Regional
- By Component
- By Deployment
- By Buyer Type
- By Use Case
- By Asset Scope
- Competition Analysis
- Competition Deep Dive
- Claroty
- Overview
- Product Portfolio
- Profitability by Market Segments (Product/Age /Sales Channel/Region)
- Sales Footprint
- Strategy Overview
- Marketing Strategy
- Product Strategy
- Channel Strategy
- Asimily
- Censinet
- Cynerio
- Armis
- Forescout
- Ordr
- Claroty
- Competition Deep Dive
- Assumptions & Acronyms Used
List of Tables
- Table 1: Global Market Value (USD Million) Forecast by Region, 2021 to 2036
- Table 2: Global Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 3: Global Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 4: Global Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 5: Global Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 6: Global Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 7: North America Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 8: North America Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 9: North America Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 10: North America Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 11: North America Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 12: North America Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 13: Latin America Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 14: Latin America Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 15: Latin America Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 16: Latin America Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 17: Latin America Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 18: Latin America Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 19: Western Europe Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 20: Western Europe Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 21: Western Europe Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 22: Western Europe Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 23: Western Europe Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 24: Western Europe Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 25: Eastern Europe Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 26: Eastern Europe Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 27: Eastern Europe Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 28: Eastern Europe Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 29: Eastern Europe Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 30: Eastern Europe Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 31: East Asia Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 32: East Asia Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 33: East Asia Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 34: East Asia Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 35: East Asia Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 36: East Asia Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 37: South Asia and Pacific Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 38: South Asia and Pacific Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 39: South Asia and Pacific Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 40: South Asia and Pacific Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 41: South Asia and Pacific Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 42: South Asia and Pacific Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
- Table 43: Middle East & Africa Market Value (USD Million) Forecast by Country, 2021 to 2036
- Table 44: Middle East & Africa Market Value (USD Million) Forecast by Component , 2021 to 2036
- Table 45: Middle East & Africa Market Value (USD Million) Forecast by Deployment, 2021 to 2036
- Table 46: Middle East & Africa Market Value (USD Million) Forecast by Buyer Type, 2021 to 2036
- Table 47: Middle East & Africa Market Value (USD Million) Forecast by Use Case, 2021 to 2036
- Table 48: Middle East & Africa Market Value (USD Million) Forecast by Asset Scope, 2021 to 2036
List of Figures
- Figure 1: Global Market Pricing Analysis
- Figure 2: Global Market Value (USD Million) Forecast 2021-2036
- Figure 3: Global Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 4: Global Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 5: Global Market Attractiveness Analysis by Component
- Figure 6: Global Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 7: Global Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 8: Global Market Attractiveness Analysis by Deployment
- Figure 9: Global Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 10: Global Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 11: Global Market Attractiveness Analysis by Buyer Type
- Figure 12: Global Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 13: Global Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 14: Global Market Attractiveness Analysis by Use Case
- Figure 15: Global Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 16: Global Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 17: Global Market Attractiveness Analysis by Asset Scope
- Figure 18: Global Market Value (USD Million) Share and BPS Analysis by Region, 2026 and 2036
- Figure 19: Global Market Y-o-Y Growth Comparison by Region, 2026-2036
- Figure 20: Global Market Attractiveness Analysis by Region
- Figure 21: North America Market Incremental Dollar Opportunity, 2026-2036
- Figure 22: Latin America Market Incremental Dollar Opportunity, 2026-2036
- Figure 23: Western Europe Market Incremental Dollar Opportunity, 2026-2036
- Figure 24: Eastern Europe Market Incremental Dollar Opportunity, 2026-2036
- Figure 25: East Asia Market Incremental Dollar Opportunity, 2026-2036
- Figure 26: South Asia and Pacific Market Incremental Dollar Opportunity, 2026-2036
- Figure 27: Middle East & Africa Market Incremental Dollar Opportunity, 2026-2036
- Figure 28: North America Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 29: North America Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 30: North America Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 31: North America Market Attractiveness Analysis by Component
- Figure 32: North America Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 33: North America Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 34: North America Market Attractiveness Analysis by Deployment
- Figure 35: North America Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 36: North America Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 37: North America Market Attractiveness Analysis by Buyer Type
- Figure 38: North America Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 39: North America Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 40: North America Market Attractiveness Analysis by Use Case
- Figure 41: North America Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 42: North America Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 43: North America Market Attractiveness Analysis by Asset Scope
- Figure 44: Latin America Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 45: Latin America Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 46: Latin America Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 47: Latin America Market Attractiveness Analysis by Component
- Figure 48: Latin America Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 49: Latin America Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 50: Latin America Market Attractiveness Analysis by Deployment
- Figure 51: Latin America Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 52: Latin America Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 53: Latin America Market Attractiveness Analysis by Buyer Type
- Figure 54: Latin America Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 55: Latin America Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 56: Latin America Market Attractiveness Analysis by Use Case
- Figure 57: Latin America Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 58: Latin America Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 59: Latin America Market Attractiveness Analysis by Asset Scope
- Figure 60: Western Europe Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 61: Western Europe Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 62: Western Europe Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 63: Western Europe Market Attractiveness Analysis by Component
- Figure 64: Western Europe Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 65: Western Europe Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 66: Western Europe Market Attractiveness Analysis by Deployment
- Figure 67: Western Europe Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 68: Western Europe Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 69: Western Europe Market Attractiveness Analysis by Buyer Type
- Figure 70: Western Europe Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 71: Western Europe Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 72: Western Europe Market Attractiveness Analysis by Use Case
- Figure 73: Western Europe Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 74: Western Europe Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 75: Western Europe Market Attractiveness Analysis by Asset Scope
- Figure 76: Eastern Europe Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 77: Eastern Europe Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 78: Eastern Europe Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 79: Eastern Europe Market Attractiveness Analysis by Component
- Figure 80: Eastern Europe Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 81: Eastern Europe Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 82: Eastern Europe Market Attractiveness Analysis by Deployment
- Figure 83: Eastern Europe Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 84: Eastern Europe Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 85: Eastern Europe Market Attractiveness Analysis by Buyer Type
- Figure 86: Eastern Europe Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 87: Eastern Europe Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 88: Eastern Europe Market Attractiveness Analysis by Use Case
- Figure 89: Eastern Europe Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 90: Eastern Europe Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 91: Eastern Europe Market Attractiveness Analysis by Asset Scope
- Figure 92: East Asia Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 93: East Asia Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 94: East Asia Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 95: East Asia Market Attractiveness Analysis by Component
- Figure 96: East Asia Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 97: East Asia Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 98: East Asia Market Attractiveness Analysis by Deployment
- Figure 99: East Asia Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 100: East Asia Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 101: East Asia Market Attractiveness Analysis by Buyer Type
- Figure 102: East Asia Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 103: East Asia Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 104: East Asia Market Attractiveness Analysis by Use Case
- Figure 105: East Asia Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 106: East Asia Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 107: East Asia Market Attractiveness Analysis by Asset Scope
- Figure 108: South Asia and Pacific Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 109: South Asia and Pacific Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 110: South Asia and Pacific Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 111: South Asia and Pacific Market Attractiveness Analysis by Component
- Figure 112: South Asia and Pacific Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 113: South Asia and Pacific Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 114: South Asia and Pacific Market Attractiveness Analysis by Deployment
- Figure 115: South Asia and Pacific Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 116: South Asia and Pacific Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 117: South Asia and Pacific Market Attractiveness Analysis by Buyer Type
- Figure 118: South Asia and Pacific Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 119: South Asia and Pacific Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 120: South Asia and Pacific Market Attractiveness Analysis by Use Case
- Figure 121: South Asia and Pacific Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 122: South Asia and Pacific Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 123: South Asia and Pacific Market Attractiveness Analysis by Asset Scope
- Figure 124: Middle East & Africa Market Value Share and BPS Analysis by Country, 2026 and 2036
- Figure 125: Middle East & Africa Market Value Share and BPS Analysis by Component , 2026 and 2036
- Figure 126: Middle East & Africa Market Y-o-Y Growth Comparison by Component , 2026-2036
- Figure 127: Middle East & Africa Market Attractiveness Analysis by Component
- Figure 128: Middle East & Africa Market Value Share and BPS Analysis by Deployment, 2026 and 2036
- Figure 129: Middle East & Africa Market Y-o-Y Growth Comparison by Deployment, 2026-2036
- Figure 130: Middle East & Africa Market Attractiveness Analysis by Deployment
- Figure 131: Middle East & Africa Market Value Share and BPS Analysis by Buyer Type, 2026 and 2036
- Figure 132: Middle East & Africa Market Y-o-Y Growth Comparison by Buyer Type, 2026-2036
- Figure 133: Middle East & Africa Market Attractiveness Analysis by Buyer Type
- Figure 134: Middle East & Africa Market Value Share and BPS Analysis by Use Case, 2026 and 2036
- Figure 135: Middle East & Africa Market Y-o-Y Growth Comparison by Use Case, 2026-2036
- Figure 136: Middle East & Africa Market Attractiveness Analysis by Use Case
- Figure 137: Middle East & Africa Market Value Share and BPS Analysis by Asset Scope, 2026 and 2036
- Figure 138: Middle East & Africa Market Y-o-Y Growth Comparison by Asset Scope, 2026-2036
- Figure 139: Middle East & Africa Market Attractiveness Analysis by Asset Scope
- Figure 140: Global Market - Tier Structure Analysis
- Figure 141: Global Market - Company Share Analysis