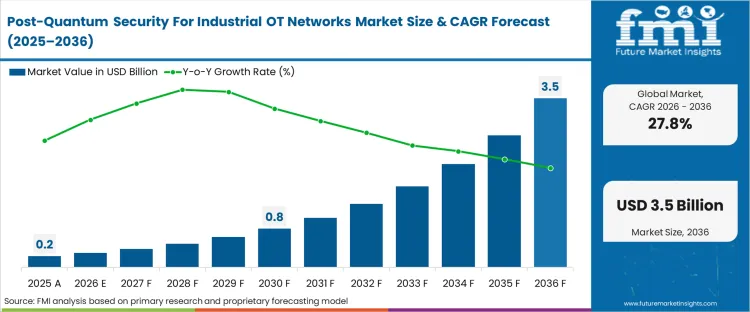
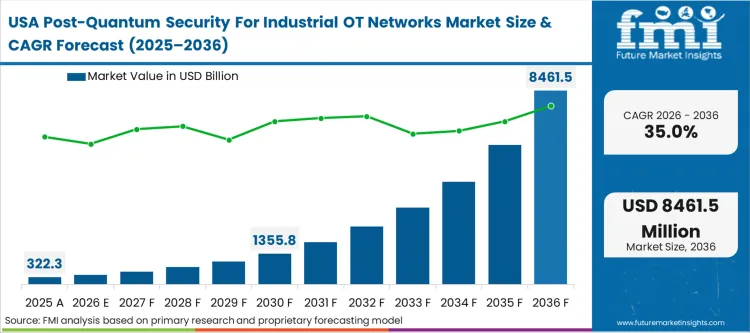
The post-quantum OT cybersecurity market size expanded at USD 0.2 billion in 2025. The industry growth is expected to reach USD 0.3 billion in 2026 at a CAGR of 27.8% during the forecast period. Predicted to consistently incline towards a significant valuation of USD 3.0 billion through 2036 as critical infrastructure operators face a structural mandate to secure industrial control assets that will physically outlive the cryptographic relevance of current encryption standards.
Asset owners are actively shifting from theoretical threat modeling to immediate cryptographic inventory mapping to mitigate the harvest now decrypt later OT risk. The core decision centers on whether to overlay new protocols onto existing legacy networks or wait for native integration within next-generation programmable logic controllers. Waiting forces operators to accept an unquantifiable vulnerability window because data harvesting attacks actively target long-lived industrial telemetry. Moving forward early requires navigating a fragmented landscape of hybrid algorithms. Evaluating post quantum cryptography migration pathways reveals that resilient operators implement crypto-agility in OT networks PQC by decoupling their cryptographic foundation from the underlying hardware lifecycle, allowing them to swap algorithms without disrupting continuous physical processes.
The structural gate triggering mass deployment is the formal release of finalized lattice-based algorithms by federal cryptography bodies. Once these mathematical blueprints move from draft to finalized standard, the liability calculus for corporate boards shifts instantly. Procurement teams subsequently mandate these finalized algorithms as baseline requirements for all new operational technology contracts, permanently altering the barriers to entry for industrial component manufacturers.
The United States is projected to advance at 35.0%, followed closely by India tracking at 33.0%. China is anticipated to post 32.0%, while Japan follows at 30.0%. South Korea is estimated to expand at 29.0%, Germany is likely to register 28.0%, and the United Kingdom is forecast to grow at 25.0%. This divergence reflects variations in national critical infrastructure protection mandates rather than organic technological absorption rates. Regions with rigid federal compliance calendars force their utility sectors to transition earlier, whereas regions dependent on voluntary adoption lag behind the global baseline.
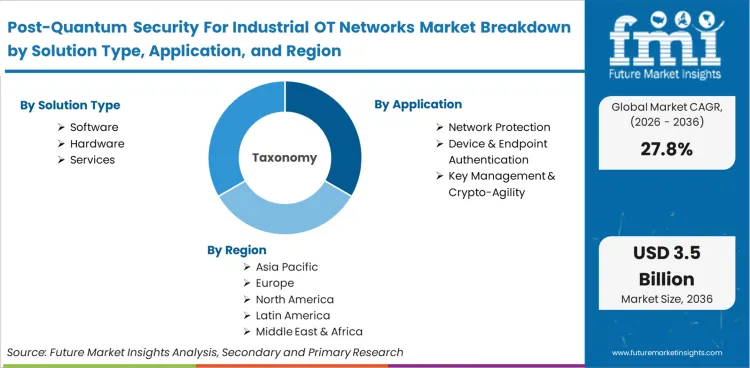
The industry encompasses cryptographic software, hardware accelerators, and integration services specifically engineered to protect operational technology against decryption by advanced computing threats. It focuses on the distinct operational constraints of industrial environments, prioritizing deterministic latency, low-compute device compatibility, and uninterrupted physical processes over conventional enterprise IT data throughput metrics, defining the core of PQC for industrial control systems.
Scope includes quantum-resistant algorithms implemented on industrial endpoints, hardware security modules designed for supervisory architecture, crypto-agile key management servers, and specialized firmware signing protocols. It integrates directly with quantum cryptography frameworks that accommodate the rigid timing and memory limitations inherent in distributed control systems and remote terminal units across critical infrastructure, validating the scope of post quantum cryptography OT networks.
General enterprise IT cryptographic solutions are explicitly excluded. Standalone quantum hardware and consumer-grade encryption software are strictly outside the boundary. These technologies fail to address the ruggedization, protocol-specific routing, and deterministic response requirements of operational technology, making them functionally incompatible with the industrial control ecosystem.
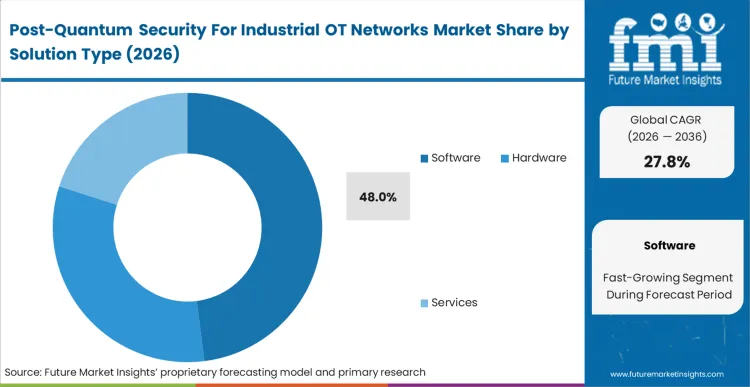
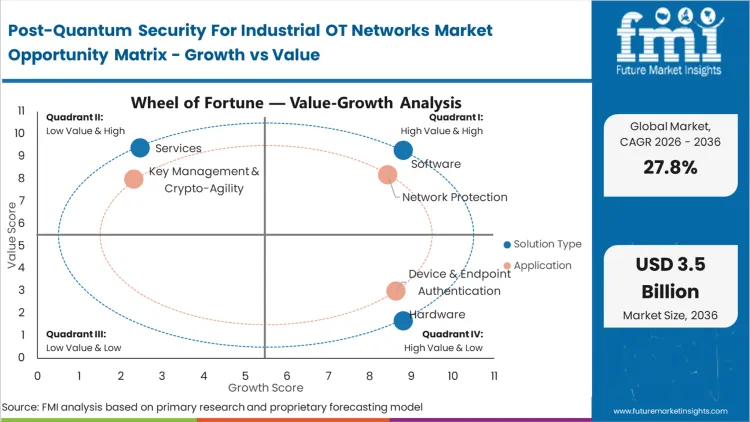
The challenges migrating OT to post-quantum cryptography dictate that operators cannot rip and replace their entire physical plant, which is why Software captures a dominant 48.0% share in 2026. FMI analysts opine that deploying cryptographic software overlays allows facilities to upgrade their defensive posture without decommissioning functional hardware. Buyers initiate this process by evaluating hardware security module compatibility, ensuring that new code can operate within existing processors. When software successfully bridges the gap, incorporating PQC firmware signing OT devices into legacy endpoints, operators validate the choice by measuring network latency impact. The lifecycle economics heavily favor software updates over physical module replacements. Those who mandate hardware-only transitions face massive capital expenditures and unacceptable downtime across their production lines.
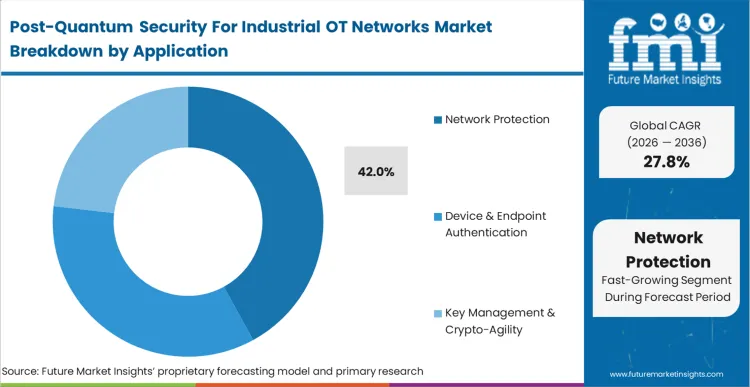
Based on FMI's assessment, securing the communication pipeline prevents attackers from manipulating sensor data in transit. Buyers rely on robust access control mechanisms integrated into network switches to enforce strict cryptographic boundaries. When the network itself handles the encryption load, the computational burden on aging programmable logic controllers is significantly reduced. Operators who attempt to push this cryptographic heavy lifting directly onto legacy devices routinely trigger cascading operational failures. Legacy boundary firewalls fail to protect the internal east-west traffic flowing between industrial controllers, forcing a rapid shift toward dedicated internal protection. Network Protection holds 42.0% share in 2026 because encrypting the transport layer using post-quantum key encapsulation OT networks is the most immediate way to secure telemetry without touching the fragile logic running on the actual endpoints.
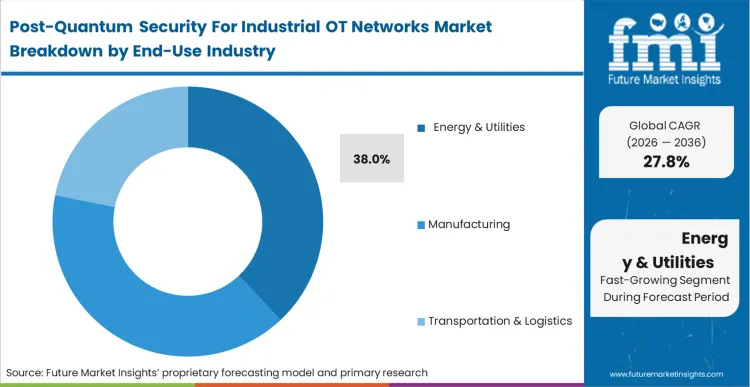
Procurement directors at power plants and grid operators face an immediate regulatory mandate to harden their communication infrastructure against advanced decryption capabilities. Energy & Utilities secures 38.0% share in 2026 as grid modernization projects explicitly require crypto-agility features. According to FMI's estimates, the integration of operational technology security directly into substation designs means post-quantum security applications in energy OT networks push performance well beyond standard industrial requirements. These environments demand encryption that can survive extreme physical conditions and electrical interference while maintaining perfect synchronization. The post-quantum OT security energy utilities face stringent qualification standards from national grid authorities that determine exactly which cryptographic vendors are permitted to participate in critical infrastructure tenders. Facilities that attempt to utilize generic enterprise solutions quickly discover performance gaps during grid load balancing events.
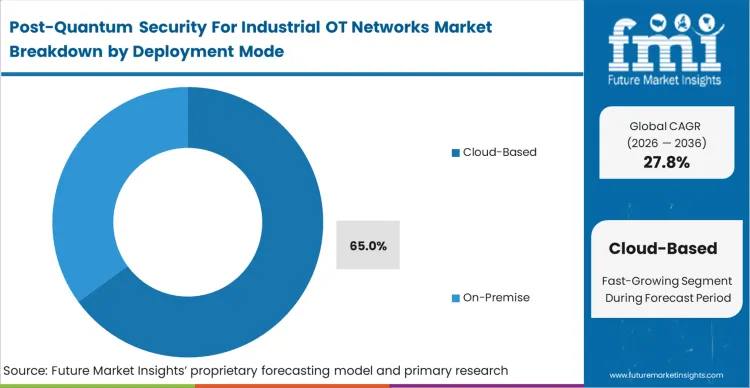
In FMI's view, maintaining localized cryptographic authority eliminates the recurring data egress costs associated with cloud architectures. The upfront capital expenditure of deploying local servers is rapidly offset by the elimination of external connectivity risks and total lifecycle cost comparison strongly favors localized control for continuous manufacturing processes. Plant managers who attempt to route critical key exchanges through external cloud providers expose their facilities to immediate production halts during routine internet service disruptions. The strict isolation requirements of physical production environments mean that cloud-based key management introduces unacceptable external dependencies. On-Premise deployment leads this dimension because industrial operators refuse to tie the continuous operation of their local machinery to the availability of an external internet connection.
The transition toward verifiable cryptographic resilience, accelerated by the NIST PQC impact on industrial OT networks, compels procurement directors to fundamentally alter their hardware qualification criteria. The industrial cyber security landscape no longer tolerates static encryption protocols that cannot be upgraded over the air. Operators following CISA PQC OT guidance aggressively qualify vendors capable of delivering dynamic key management systems. The commercial stakes are absolute, operators either embed upgradeable encryption now or commit to replacing millions of dollars of hardware prematurely when current algorithms are officially deprecated.
The most significant structural barrier to immediate deployment remains the severe physical memory constraint inherent in existing supervisory architectures. Legacy programmable logic controllers simply lack the RAM and processing power required to execute complex lattice-based cryptography. This limitation is hard-coded into the silicon, meaning it cannot be resolved through a simple software patch. While lightweight cryptographic protocols are emerging to address this gap, their delayed standardization creates a massive holding pattern for facility engineers.
Global adoption of post-quantum security across industrial networks reveals a sharp geographic divide, heavily dictated by regional regulatory mandates and infrastructure scaling strategies. While Western regions prioritize aggressive federal compliance deadlines, Eastern markets are embedding crypto-agility directly into rapid greenfield capacity expansions. The landscape is segmented into North America, Europe, Asia Pacific, and other key territories across 40 plus countries.
.webp)
| Country | CAGR (2026 to 2036) |
|---|---|
| United States | 35.0% |
| India | 33.0% |
| China | 32.0% |
| Japan | 30.0% |
| South Korea | 29.0% |
| Germany | 28.0% |
| United Kingdom | 25.0% |
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
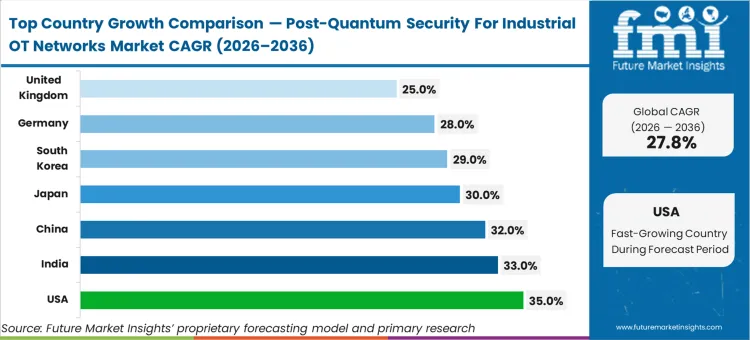
Across the region, voluntary cybersecurity frameworks are rapidly being replaced by rigid procurement deadlines set by federal policies. Upgrades here are not triggered by organic technological maturity; instead, they are executed to strictly comply with aggressive national security directives. FMI analysts opine that this policy-led environment forces a highly concentrated procurement cycle, as government agencies demand that suppliers of critical systems provide a verifiable pathway toward cryptographic modernization.
FMI assesses, North America’s trajectory remains inextricably tied to government policy, creating an environment where vendor success depends entirely on navigating and anticipating federal compliance milestones.
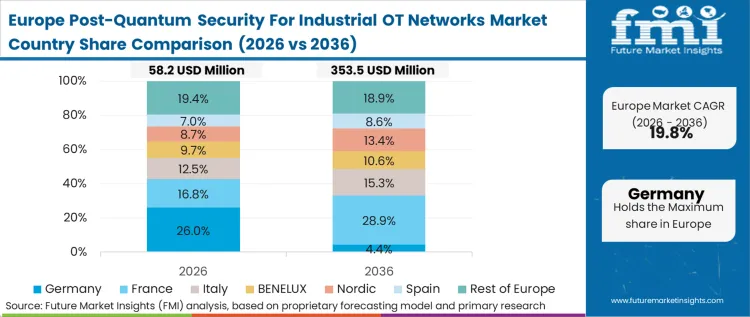
Standardized cryptographic protocols are an absolute necessity across Europe's dense network of multinational manufacturing hubs and cross-border energy grids. Grid operators throughout the region face the intricate challenge of ensuring that localized security enhancements in one country do not break deterministic communications with neighboring power networks. As per FMI's projection, this infrastructure-led ecosystem necessitates exhaustive interoperability testing before the deployment of any new algorithm. As a result, procurement consortiums show a massive preference for vendors who can demonstrate flawless cross-border key management capabilities.
As per FMI’s estimates, the European landscape is defined by the absolute necessity of interoperability, where ensuring seamless deterministic performance across borders outweighs the rapid rollout of isolated security patches.
Across rapidly scaling manufacturing hubs, the evaluation of cryptographic transition timelines is heavily influenced by aggressive capacity expansion goals and underlying cost structures. Facility directors prioritize security frameworks that can be rolled out on a massive scale without causing a disproportionate spike in the unit cost of connected endpoints. Based on FMI's assessment, this intensely economics-led environment overwhelmingly favors software-defined overlays that utilize existing network hardware rather than relying on costly physical security modules.
FMI's report includes extensive coverage of additional territories across the Middle East and Latin America. These emerging industrial security system segments largely bypass intermediate security architectures, adopting fully crypto-agile frameworks as their baseline standard during initial infrastructure build-outs.
Analyzing OT cybersecurity vs post-quantum security reveals that the landscape is highly concentrated because providing cryptographic protection for operational technology requires an extremely rare combination of advanced mathematical expertise and deep industrial engineering knowledge. When procurement teams compare post-quantum OT security vendors, they do not select based on theoretical algorithm strength; they evaluate strictly on proven ability to integrate encryption into deterministic operational technology without causing physical process interruptions. Companies like Siemens AG and Rockwell Automation Inc. leverage their massive installed base to dictate how security overlays interact with physical controllers. The primary variable separating qualified vendors from the unqualified is the possession of certified interoperability with legacy supervisory control systems.
Incumbents maintain their advantage because rewriting the core communication protocols of industrial equipment is an incredibly slow and risk-averse process. Established players possess decades of proprietary protocol knowledge that cannot be quickly replicated. Looking closely at PQC OT security vendors 2025, a challenger attempting to break into this space must build highly specific protocol translation capabilities. They must offer solutions that bridge the gap between classic environments and modern requirements without adding latency. Providing specialized quantum key distribution test equipment helps emerging firms prove the efficacy of their algorithms in simulated industrial settings.
Large utility buyers actively resist vendor lock-in by demanding adherence to open cryptographic standards rather than proprietary encryption schemes. They leverage their immense purchasing power to force dominant equipment manufacturers to support third-party key management servers. The structural tension between utility demands for interoperability and vendor incentives to create closed ecosystems dictates the pace of product development. Through 2036, the market becomes increasingly consolidated as established industrial automation giants acquire specialized cryptographic startups to internalize advanced mathematical capabilities.
| Metric | Value |
|---|---|
| Quantitative Units | USD 0.3 billion to USD 3.0 billion, at a CAGR of 27.8% |
| Market Definition | The specialized cryptographic ecosystem engineered to protect industrial control systems against advanced decryption threats, prioritizing deterministic latency and low-compute device compatibility over standard IT metrics. |
| Solution Type Segmentation | Software, Hardware, Services |
| Application Segmentation | Network Protection, Device & Endpoint Authentication, Key Management & Crypto-Agility, Code Signing & Firmware Integrity |
| End-Use Industry Segmentation | Energy & Utilities, Manufacturing, Transportation & Logistics, Chemical & Process Industries |
| Deployment Mode Segmentation | On-Premise, Cloud-Based |
| Regions Covered | North America, Europe, Asia Pacific |
| Countries Covered | United States, China, Germany, Japan, United Kingdom, India, South Korea, and 40 plus countries |
| Key Companies Profiled | PQShield Ltd., BTQ Technologies Corp., QuSecure Inc., Siemens AG., Honeywell International Inc., Rockwell Automation Inc., Cisco Systems Inc. |
| Forecast Period | 2026 to 2036 |
| Approach | Primary interviews were conducted with industrial control security architects and cryptographic transition officers. The baseline data anchors to the volume of critical endpoints requiring cryptographic upgrades. Forecasts were cross-validated against published standards and industrial vendor product roadmaps. |
Source: Future Market Insights (FMI) analysis, based on proprietary forecasting model and primary research
This bibliography is provided for reader reference. The full FMI report contains the complete reference list with primary source documentation.
How large is the post-quantum OT cybersecurity ecosystem in 2026?
The sector is anticipated to reach USD 0.3 billion in 2026 as tier-one critical infrastructure operators deploy foundational software overlays.
What will it be valued at by 2036?
The valuation is projected to reach USD 3.0 billion by 2036, marking the point where crypto-agility becomes a mandatory, integrated feature of all new industrial equipment.
What CAGR is projected?
A CAGR of 27.8% is expected during the forecast period as rigid federal compliance deadlines force operators to execute comprehensive upgrades rapidly.
Which Solution Type segment leads?
Software is poised to lead with 48.0% share in 2026 because it allows operators to overlay modern encryption without taking functional physical machinery offline.
Which Application segment leads?
Network Protection is expected to dominate with 42.0% share in 2026 by securing communication pipelines between controllers to defend against data harvesting.
Which End-Use Industry segment leads?
Energy & Utilities is set to hold 38.0% share in 2026 due to explicit national security directives compelling the power grid to modernize its cryptographic posture earliest.
What drives rapid growth?
The long operational lifecycles of industrial assets force utility managers to secure equipment installed today against the decryption capabilities adversaries will possess a decade from now.
What is the primary restraint?
The severe memory and compute limitations of legacy programmable logic controllers prevent the processing of larger lattice-based key sizes, halting upgrades until protocol translation gateways are engineered.
Which country grows fastest?
The United States is projected to grow at 35.0% because its procurement is driven by hard federal mandates tied directly to government contracting eligibility.
How to migrate OT networks to post-quantum cryptography effectively?
Asset owners must decouple their encryption layer from hardware lifecycles by deploying software overlays on non-critical nodes before replacing legacy programmable logic controllers.
What are the best post-quantum solutions for OT industrial networks?
The most effective solutions deploy inline, software-defined network protection that handles encryption directly at the switch level to shield computationally weak legacy endpoints.
What is the expected ROI of post-quantum security for industrial OT?
The return on investment is measured in avoided downtime and secured federal contracting eligibility by preventing the forced, premature replacement of hardware when current algorithms are deprecated.
How does the regulatory environment shape procurement?
Federal cryptographic transition roadmaps force utility compliance officers to align their capital expenditure planning directly with governmental algorithmic finalization dates rather than organic upgrade cycles.
How does deterministic latency impact adoption?
Security architects must rigorously test new cryptographic software to ensure the complex mathematics do not delay critical command signals by even a millisecond, which could cause physical collisions on the factory floor.
How do established industrial vendors maintain dominance?
Incumbents leverage decades of proprietary knowledge regarding legacy communication protocols, forcing emerging cryptographic startups to partner with them to integrate advanced algorithms into closed ecosystems.
Why is on-premise deployment structurally required?
Industrial operators refuse to link the continuous operation of physical machinery to external cloud availability, utilizing localized key management to eliminate the risk of production-halting internet outages.
What makes the German footprint unique in Europe?
Germany's concentration of highly synchronized automotive manufacturing establishes the region's technical baseline by demanding cryptographic solutions that guarantee microsecond precision during key exchanges.
How does China's approach differ from Western environments?
China executes coordinated, system-wide cryptographic upgrades across state-owned infrastructure, bypassing the fragmented, individual facility procurement cycles that slow deployment in Western markets.
What operational risk occurs during the transition phase?
Network engineers face the acute risk of misconfiguring protocol translation gateways during the simultaneous use of classic and post-quantum cryptography, which can inadvertently drop critical telemetry data.
Why are hardware security modules difficult to deploy?
Integrating physical security modules into legacy supervisory systems requires careful mapping of power, cooling, and physical rack space in environments never designed to house advanced cryptographic servers.
What advantage do greenfield projects offer in India?
India's rapid expansion of new smart grids allows utility planners to build crypto-agility directly into the network foundation, avoiding massive retrofitting costs and latency compromises.
How do buyers prevent future vendor lock-in?
Procurement directors aggressively mandate adherence to open, standardized cryptographic algorithms so they can swap security vendors in the future without replacing their entire control infrastructure.
What is the role of specialized chip manufacturers?
Chip designers engineer low-power cryptographic accelerators that manage the computational penalty of advanced encryption, allowing industrial sensor manufacturers to meet new security standards without increasing device size.
What makes firmware signing critical for endpoint security?
Cryptographic architects prioritize resilient signing protocols to guarantee that future over-the-air updates sent to remote terminal units cannot be compromised by advanced decryption tools injecting malicious code.
Full Research Suite comprises of:
Market outlook & trends analysis
Interviews & case studies
Strategic recommendations
Vendor profiles & capabilities analysis
5-year forecasts
8 regions and 60+ country-level data splits
Market segment data splits
12 months of continuous data updates
DELIVERED AS:
PDF EXCEL ONLINE
Thank you!
You will receive an email from our Business Development Manager. Please be sure to check your SPAM/JUNK folder too.